DNS Zone Transfers
DNS stands for Domain Name System. It is a system that translates human-readable domain names into numerical IP addresses that computers can understand. When you enter a domain name into your web browser, your computer sends a request to a DNS server to resolve the domain name into an IP address. The DNS server looks up the IP address and sends it back to your computer, which then uses the IP address to connect to the website’s server and retrieve the webpage.
There are several types of DNS records, including:
- A (Address) records: These records map a domain name to an IP address.
- CNAME (Canonical Name) records: These records map a domain name to another domain name, which can then be resolved to an IP address using an A record.
- MX (Mail Exchange) records: These records map a domain name to a mail server responsible for handling email for the domain.
- NS (Name Server) records: These records specify the name servers responsible for a domain.
- PTR (Pointer) records: These records map an IP address to a domain name.
DNS interrogation is the process of querying a DNS server to obtain information about a domain, such as its IP address or name servers.
A DNS zone transfer attack is a cyber attack in which an attacker exploits vulnerabilities in the Domain Name System (DNS) protocol or servers to copy the DNS database from one server to another. This can be used to obtain sensitive information about an organization’s internal network and servers, or to launch further attacks.
DNS zone transfers are typically used for backup or load-balancing purposes and are initiated by requesting a copy of the DNS database from a DNS server. If an attacker can gain access to this database, they can obtain a list of all the domain names and associated IP addresses within the organization’s network. This information can be used to identify and target specific servers or systems for the attack.
To prevent DNS zone transfer attacks, it is important to secure DNS servers and follow best practices for DNS configuration, such as limiting access to zone transfer requests and using secure protocols like DNSSEC.
DNS recon
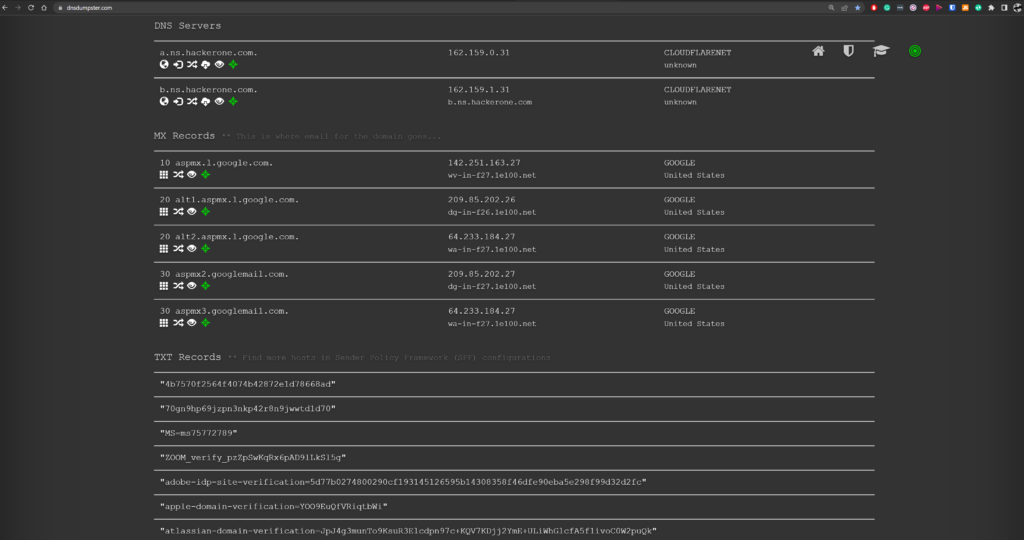
Use: https://dnsdumpster.com
DNSdumpster is a website that allows users to view DNS records for a particular domain. It is useful for a number of purposes, including:
- Identifying all the DNS records associated with a domain: DNSdumpster allows users to view all the DNS records associated with a domain, including A records, CNAME records, MX records, NS records, and PTR records. This information can be useful for identifying all the servers and services associated with a domain, as well as any potential vulnerabilities.
- Analyzing DNS configurations: DNSdumpster provides information about the DNS configuration of a domain, including the name servers being used and the DNS provider. This can be useful for identifying potential problems with the DNS configuration or for analyzing the DNS setup of a domain.
- Identifying subdomains: DNSdumpster can be used to identify subdomains of a particular domain. This can be useful for identifying hidden or unknown subdomains that might be used for malicious purposes.
- Researching a domain: DNSdumpster can be used to gather information about a domain for research or analysis purposes. For example, users might use the tool to identify the IP address of a domain or to see which name servers are being used.
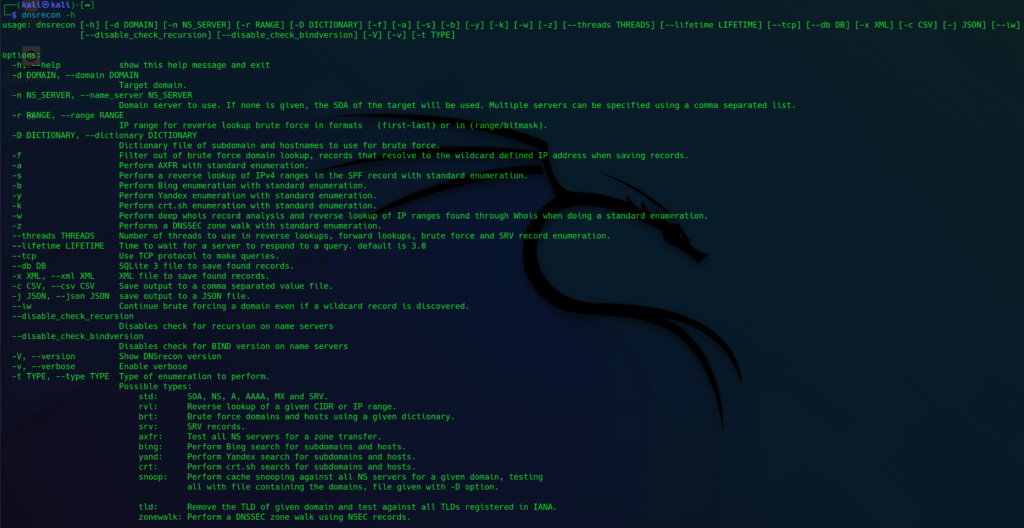
Kali Linux: dnsrecon tool
Source : https://github.com/darkoperator/dnsrecon
This script provides the ability to perform:
- Check all NS Records for Zone Transfers.
- Enumerate General DNS Records for a given Domain (MX, SOA, NS, A, AAAA, SPF, and TXT).
- Perform common SRV Record Enumeration.
- Top Level Domain (TLD) Expansion.
- Check for Wildcard Resolution.
- Brute Force subdomain and host A and AAAA records given a domain and a wordlist.
- Perform a PTR Record lookup for a given IP Range or CIDR.
- Check a DNS Server Cached records for A, AAAA, and CNAME Records provided a list of host records in a text file to check.
dnsrecon Usage Example:
┌──(kali㉿kali)-[~]
└─$ dnsrecon -d zonetransfer.me -vvv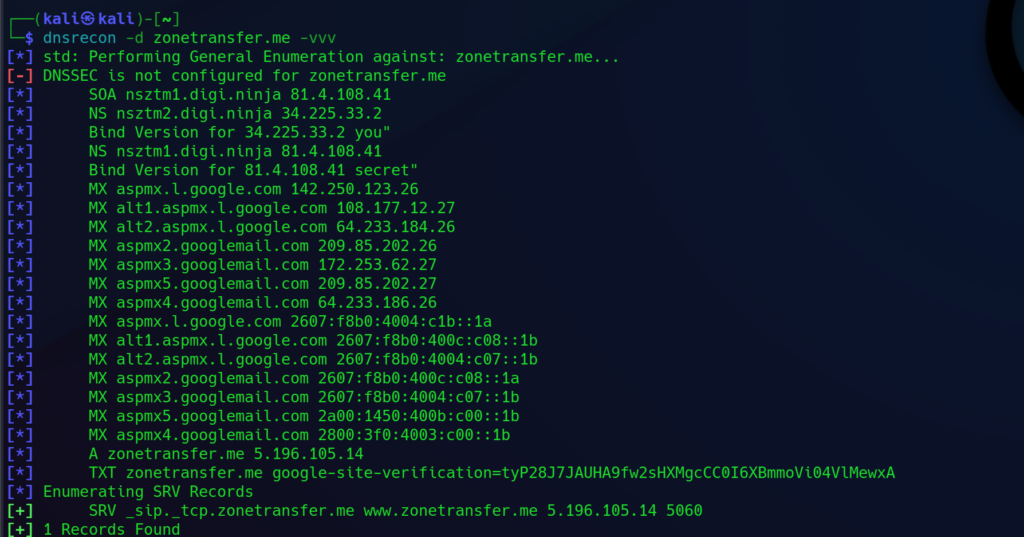
Kali Linux: dnsenum tool
DNSenum is a tool that can be used to gather information about a domain’s DNS records and subdomains. It is often used by security professionals to enumerate DNS records and perform reconnaissance during penetration testing or security assessments.
The tool can perform a variety of tasks, including:
- Performing a zone transfer to gather DNS records
- multithread script to enumerate information on a domain and to discover non-contiguous IP blocks
- Enumerating subdomains using a variety of techniques, including brute-forcing and scraping public sources
- Performing reverse lookups on IP addresses to find associated domains
- Gathering information about the DNS servers used by a domain
Source: https://github.com/SparrowOchon/dnsenum2
┌──(kali㉿kali)-[~]
└─$ dnsenum -h 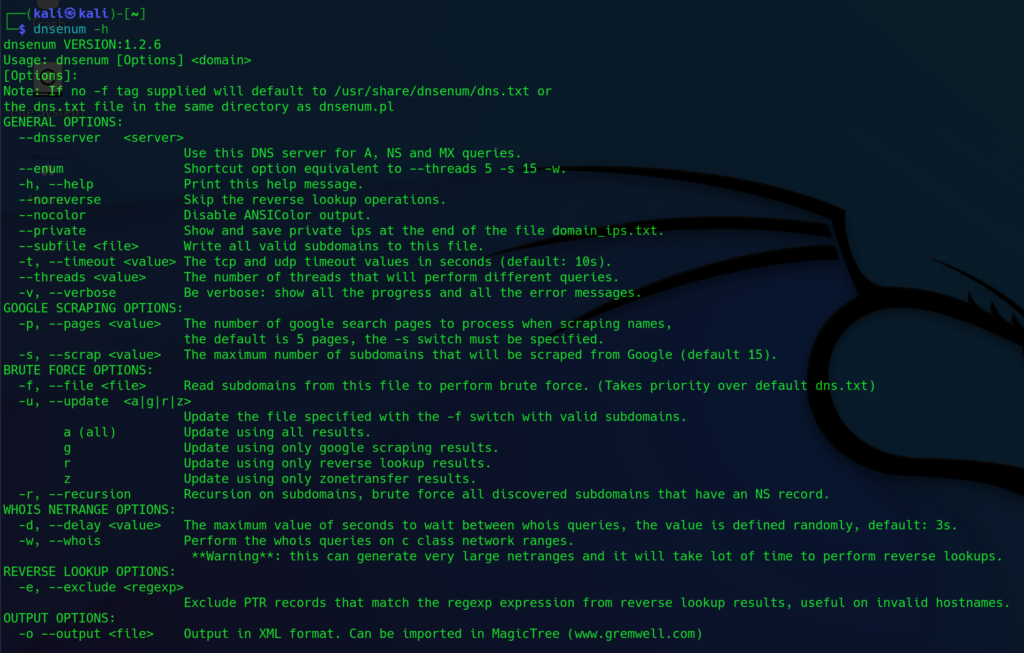
dnsenum Usage Example:
┌──(kali㉿kali)-[~]
└─$ dnsenum zonetransfer.me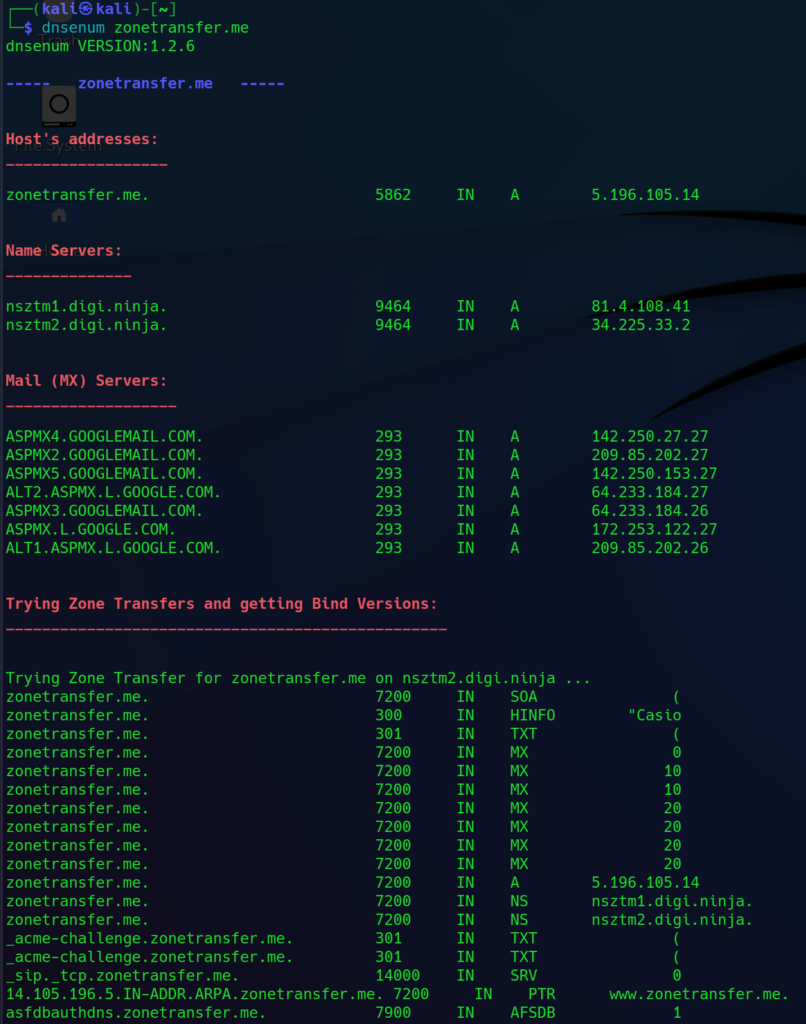
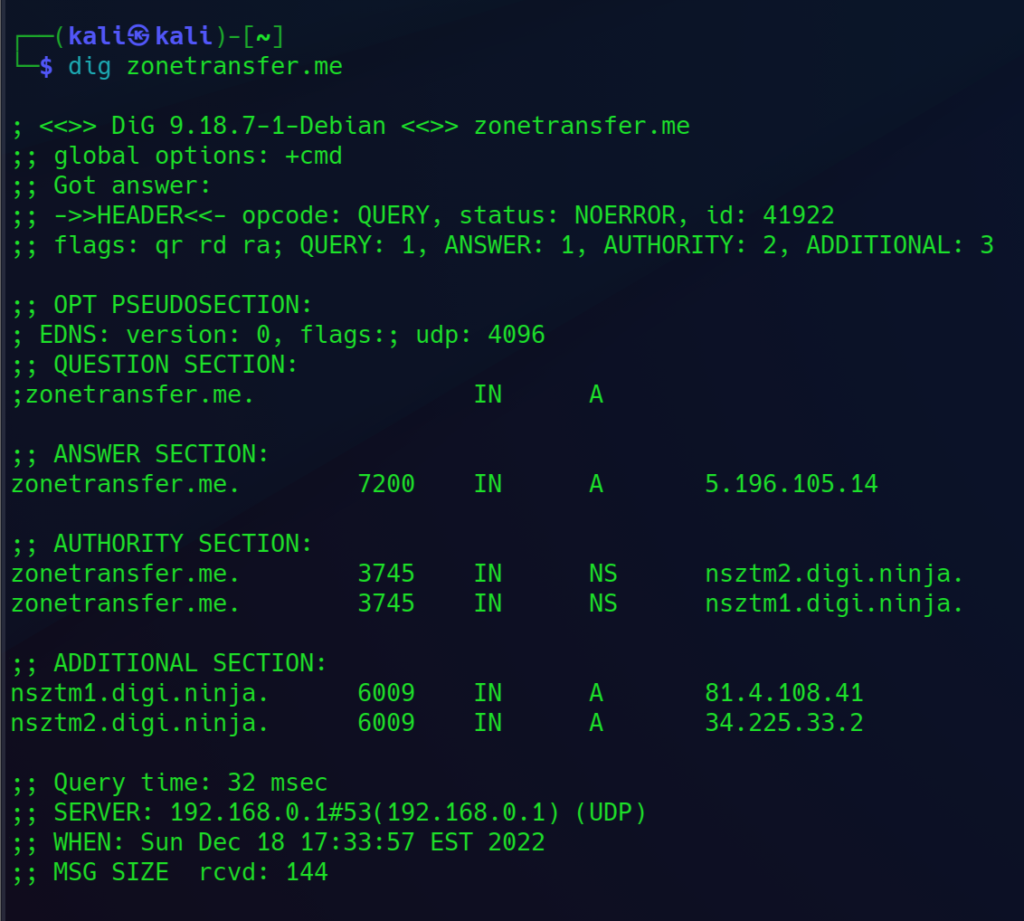
Kali Linux : dig (DNS Lookup utility) tool
The dig tool (short for Domain Information Groper) is a network utility used to query DNS (Domain Name System) name servers for information about host addresses, mail exchanges, and other DNS records. It is a command-line tool that is commonly used in Unix and Linux systems, including the Kali Linux distribution, which is a popular platform for penetration testing and security assessment.
The dig tool can be used to perform a variety of tasks, including:
- Look up the IP address associated with a domain name.
- Check the DNS records for a domain, such as A records (IP addresses), MX records (mail exchange servers), and NS records (name servers).
- Troubleshoot DNS issues by querying name servers directly and comparing the results to expected values.
- Perform reverse DNS lookups to find the domain name associated with an IP address.
To use the dig tool, you will need to specify the domain name and the type of DNS record you want to query. You can also specify the name server to query and various other options to customize the output. The dig tool is a useful tool for network administrators and security professionals to gather information about DNS configurations and troubleshoot DNS issues.
dig Usage Example:
Help:
┌──(kali㉿kali)-[~]
└─$ dig -h
┌──(kali㉿kali)-[~]
└─$ dig zonetransfer.me
Mailexchange records:
┌──(kali㉿kali)-[~]
└─$ dig zonetransfer.me -t mx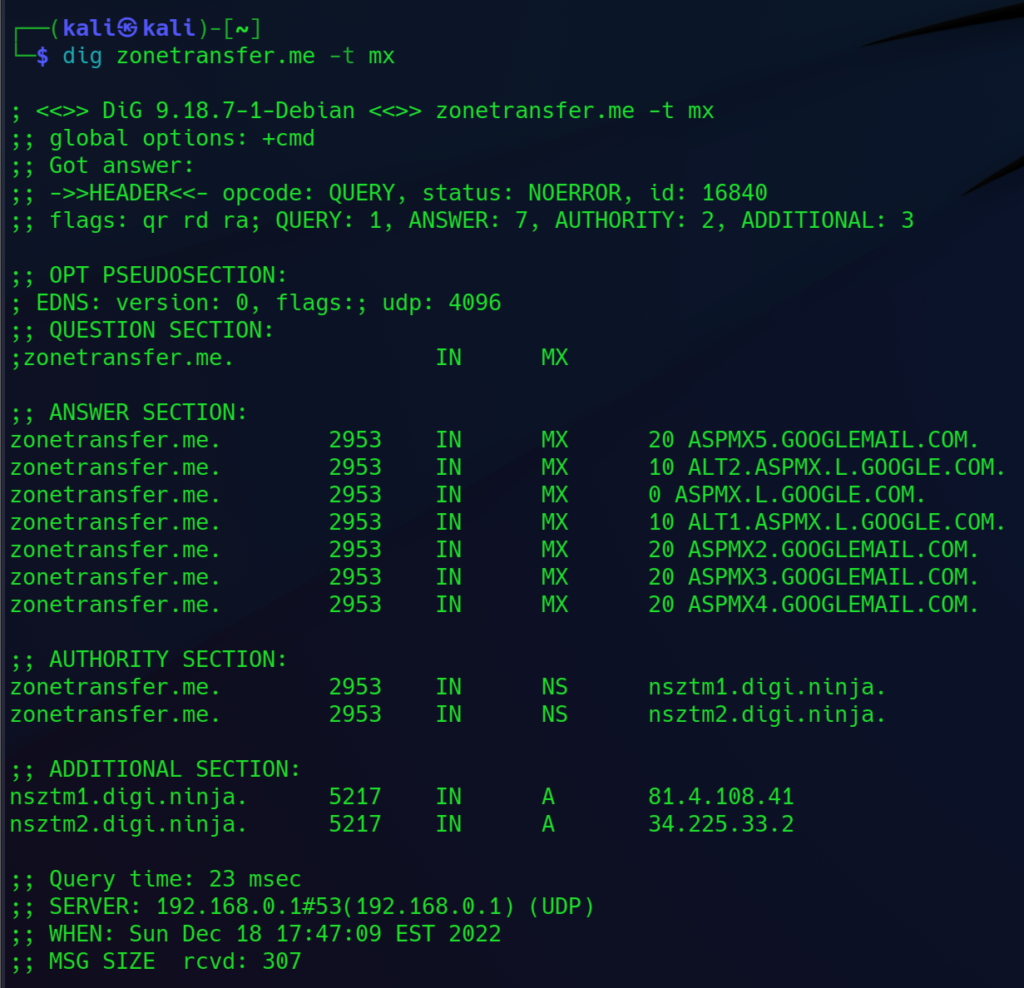
Kali Linux : fierce
Fierce is a DNS reconnaissance tool that helps locate non-contiguous IP space and hostnames against specified domains.
Fierce works by using a combination of DNS zone transfers, brute force techniques, and dictionary attacks to gather DNS information. It can be used to identify misconfigured DNS servers that allow zone transfers, which can reveal sensitive information about a network. It can also be used to discover subdomains that may not be listed in public DNS records.
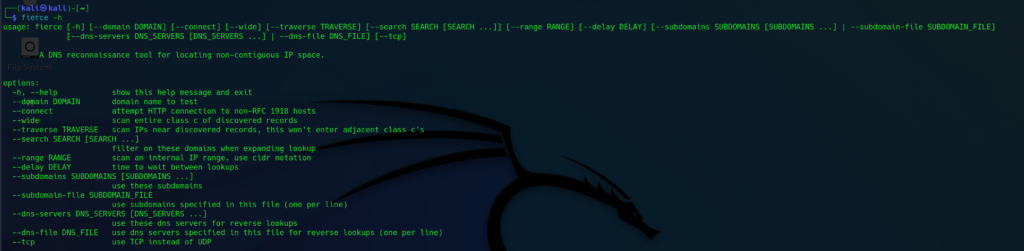
Fierce Usage Example:
Help:
┌──(kali㉿kali)-[~]
└─$ fierce -h
Example:
┌──(kali㉿kali)-[~]
└─$ fierce --domain zonetransfer.me
Host Discovery With Nmap
Nmap (Network Mapper) is a free and open-source network scanner tool that is used to discover hosts and services on a computer network by sending packets and analyzing the responses. It is used to identify active hosts on a network, determine what services are running on those hosts, and gather information about those services.
Nmap can be used for a variety of purposes, including:
- Network inventory: to gather information about the hosts and services on a network for network management purposes.
- Security assessment: to identify vulnerabilities and potential security risks on a network.
- Network mapping: to create a map of a network and its topology.
- Service detection: to identify the operating systems and services running on hosts on a network.
Nmap is available for Linux, Windows, and MacOS platforms. It is a command-line tool, but there are also graphical user interface (GUI) versions available.
Manual page of nmap : man nmap
Nmap Cheat Sheet: Commands & Examples: https://highon.coffee/blog/nmap-cheat-sheet/
To intiate host discovery scan first check your IP
Command : ip a s
Lets assume your IP address is 192.168.0.104 so You can intiate the host discovery scan on 192.168.0.0/24 to check how many hosts are their in your network
┌──(kali㉿kali)-[~]
└─$ sudo nmap -sn 192.168.0.0/24
-sn = No Port Scan
Host Discovery With netdiscover
Netdiscover is a network tool used to identify active hosts on a network. It works by sending ARP (Address Resolution Protocol) requests to all devices on the network and displaying the responses.
Source: https://github.com/netdiscover-scanner/netdiscover
Installation:
┌──(kali㉿kali)-[~]
└─$ sudo apt-get install netdiscover -y
Help:
┌──(kali㉿kali)-[~]
└─$ netdiscover -h
i = Interface
r = range
┌──(kali㉿kali)-[~]
└─$ sudo netdiscover -i eth0 -r 192.168.0.0/24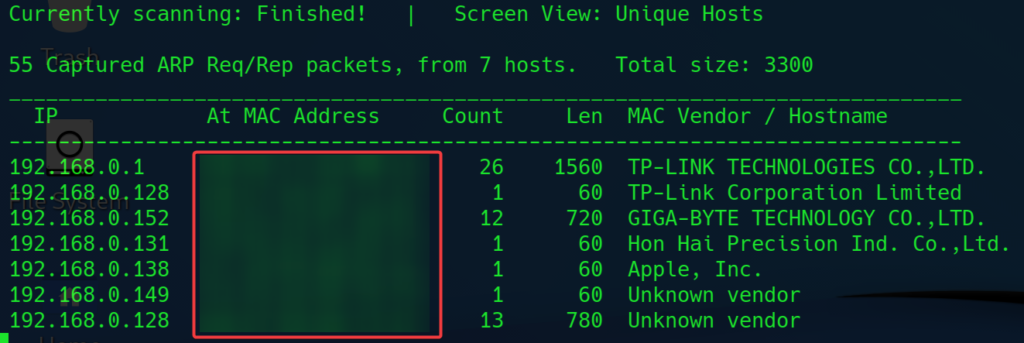
Port Scanning With Nmap
State = Filtered means either there is a firewall or port is disable
By default Nmap will perform TCP Port Scan
- To enable UDP port scan add -sU
- UDP Port Scan: nmap -Pn -sU IPAddress
TCP Port scan
Default Nmap scan, 1000 most used TCP port scan: nmap ipaddress
If host is Windows, then Windows Defender might block ping probes try using -Pn (Avoid Ping) : nmap -Pn ipaddress
Fast Nmap scan, 100 most used tcp port scan: nmap -Pn -F ipaddress
Increase the Verbosity of commands by using -v (show more outputs) : nmap -Pn -v ipaddress
-p- = will scan the entire port range 65,535: nmap -Pn -p- ipaddress
Scan custom Range: nmap -Pn -p80-65535 ipaddress
Scan specific port: nmap -Pn -p 80 ipaddress
Scan Multiple port: nmap -Pn -p 80,445,3389 ipaddress
Determine Service Version (-sV) , Service Version detection help us detect the Vulnerability in the services : nmap -p- -sV ipaddress
Operating System Detection(-O) : nmap -p- -sV -O -v ipaddress
Run nmap scripts on Open Ports to obtain more info about open ports (-sC) : nmap -p- -sV -O -sC -v ipaddress
Aggressive Scan (Combines -sV -O -sC = -A): nmap -p- -A -v ipaddress
Speed up or Slowdown Your Scan, -T<0-5>: Set timing template (higher is faster): nmap -p- -A -v -T4 ipaddress
Output Scan results
Output Normal : -oN scan.txt (save same as terminal results): nmap -p- -A -v ipaddress -oN scan.txt
Output into xml format (xml format can be imported into Metasploit ) -oX scan.xml: nmap -p- -A -v ipaddress -oX scan.xml
Supply Input list to nmap for scan: nmap -iL ips (ips = file name)





















