Website Recon and Footprinting
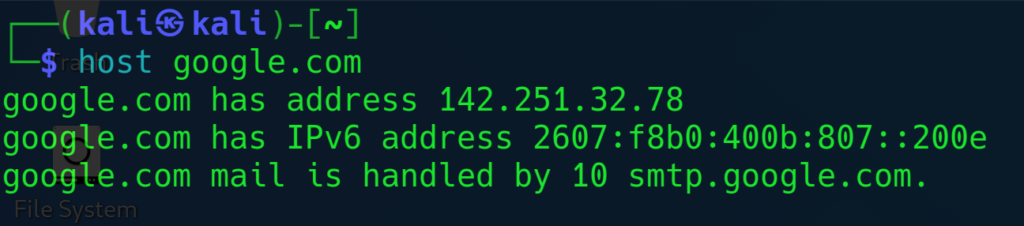
Check for the IP Address of the website
┌──(kali㉿kali)-[~]
└─$ host google.com
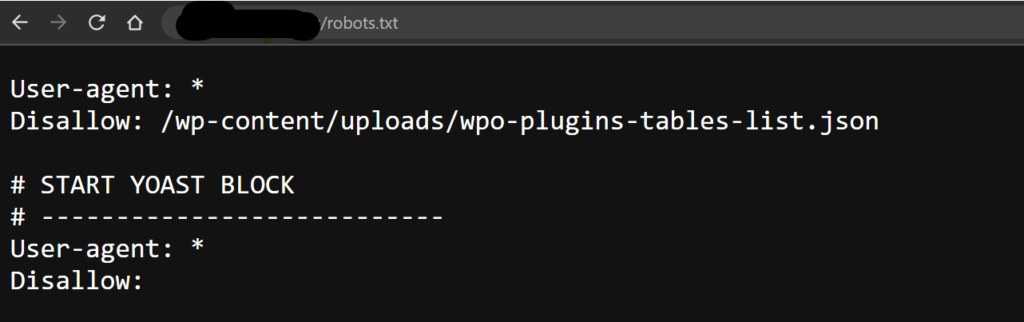
Check for the robots.txt file (website)
https://websiteurl.com/robots.txt
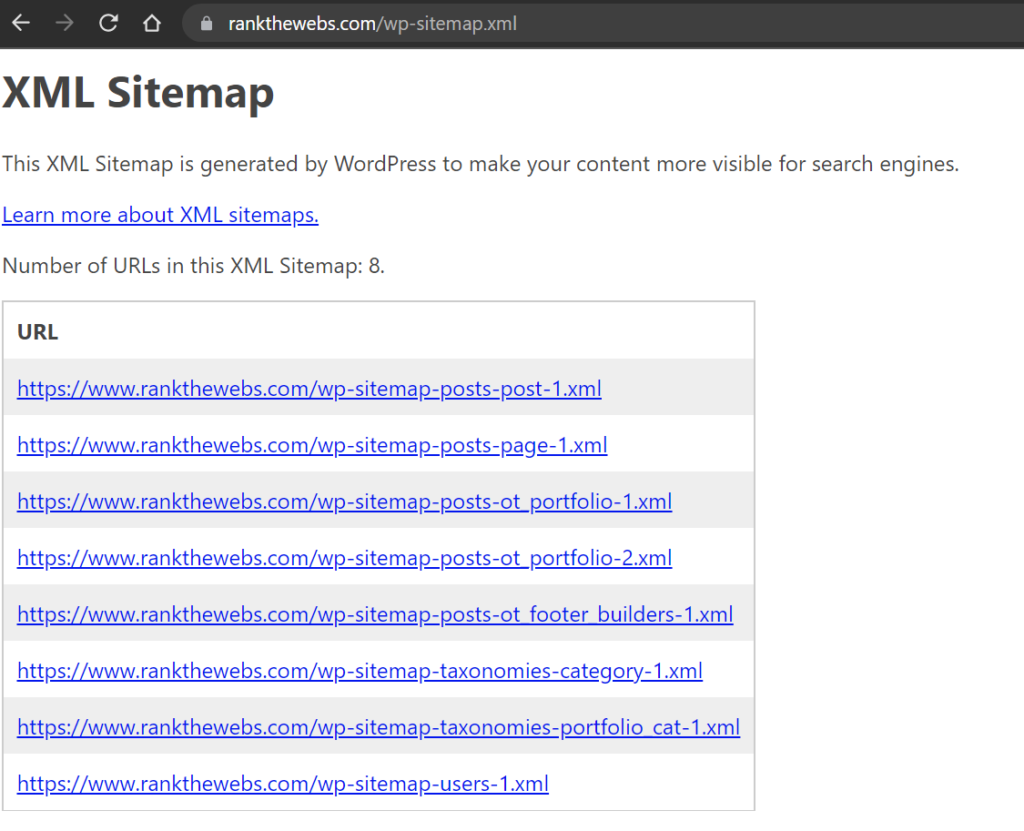
Check for sitemap.xml or sitemaps.xml
Try different variation of sitemap keyword
https://www.rankthewebs.com/sitemap.xml
or
https://www.rankthewebs.com/sitemaps.xml
or
https://www.rankthewebs.com/wp-sitemap.xml
or
https://www.rankthewebs.com/sitemap_index.xml
Identify technologies used by the website
Mozilla add-ons: Builtwith, Wappylyzer
Check if the website is behind the proxy (Cloudflare)
Help Command:
┌──(kali㉿kali)-[~]
└─$ whatweb -h
Example:
┌──(kali㉿kali)-[~]
└─$ whatweb hackerone.com
It helped us to identify hackerone.com is using Cloudflare proxy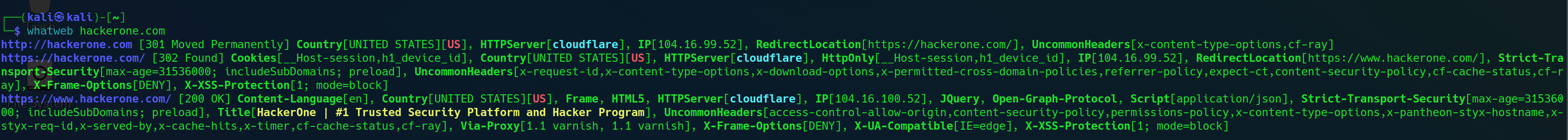
Download the Website and review the code/directories manually
Download the httrack
For Windows : Link: https://www.httrack.com/page/2/en/index.html
For Kali Linux:
┌──(kali㉿kali)-[~]
└─$ sudo apt-get install webhttrack
- after installing go to kali menu and search for httrack and it will open browser instance
Whois Enumeration
┌──(kali㉿kali)-[~]
└─$ whois hackerone.com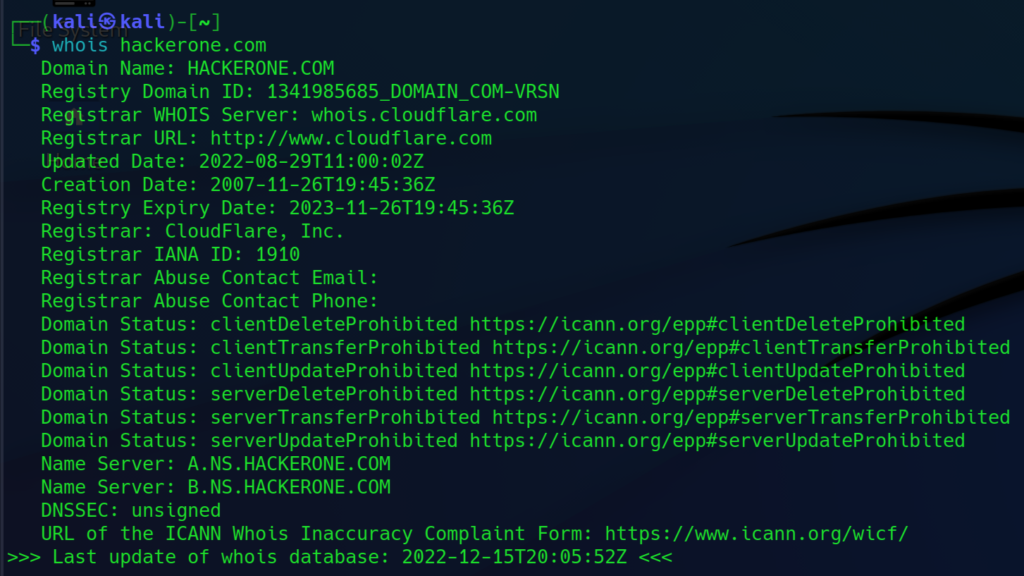
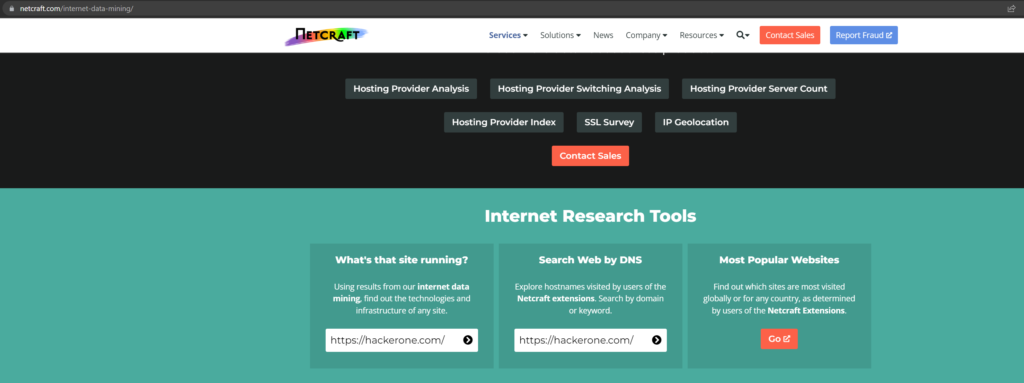
Website Footprinting
Use netcraft to check Network , DNS , DMARC , SPF , SSL Certificate Chain , Hosting History
URL : https://www.netcraft.com/internet-data-mining/
DNS Recon
Check for DNS Servers, MX Records, TXT Records ,Host (A) Records, Domain Map
Use DNSRECON tool :
Help :
┌──(kali㉿kali)-[~]
└─$ dnsrecon --help
Example:
┌──(kali㉿kali)-[~]
└─$ dnsrecon -d facebook.com
Use https://dnsdumpster.com/
Web Application Firewall (WAF) detection with wafw00f tool
wafw00f is a Web Application Firewall Fingerprinting Toolkit
┌──(kali㉿kali)-[~]
└─$ wafw00f -l
┌──(kali㉿kali)-[~]
└─$ wafw00f hackerone.com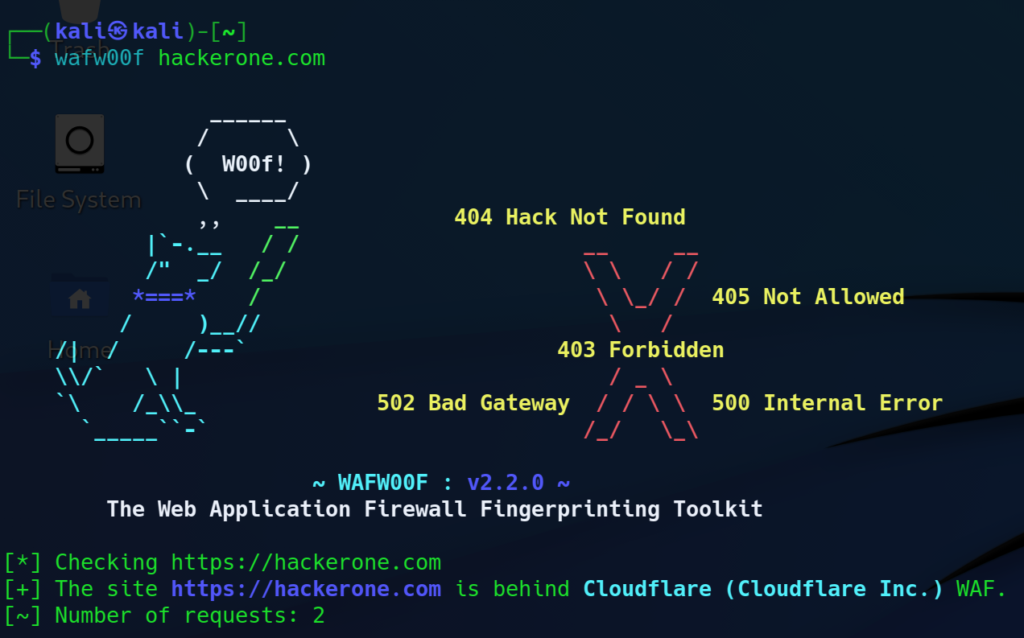
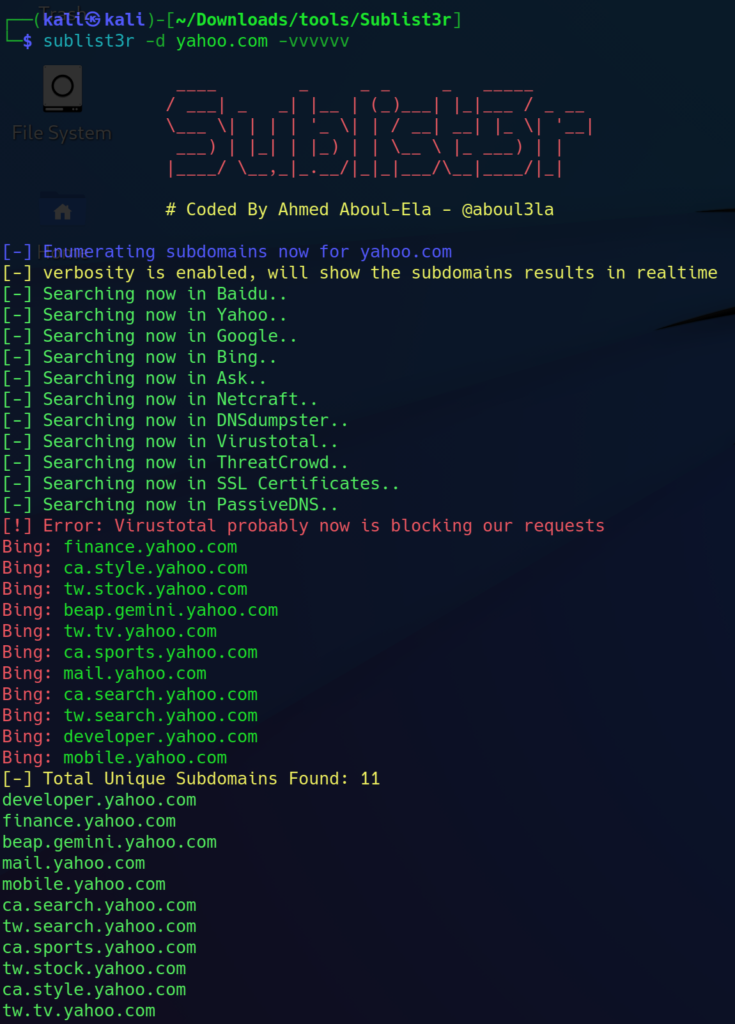
Subdomain enumeration with Sublist3r
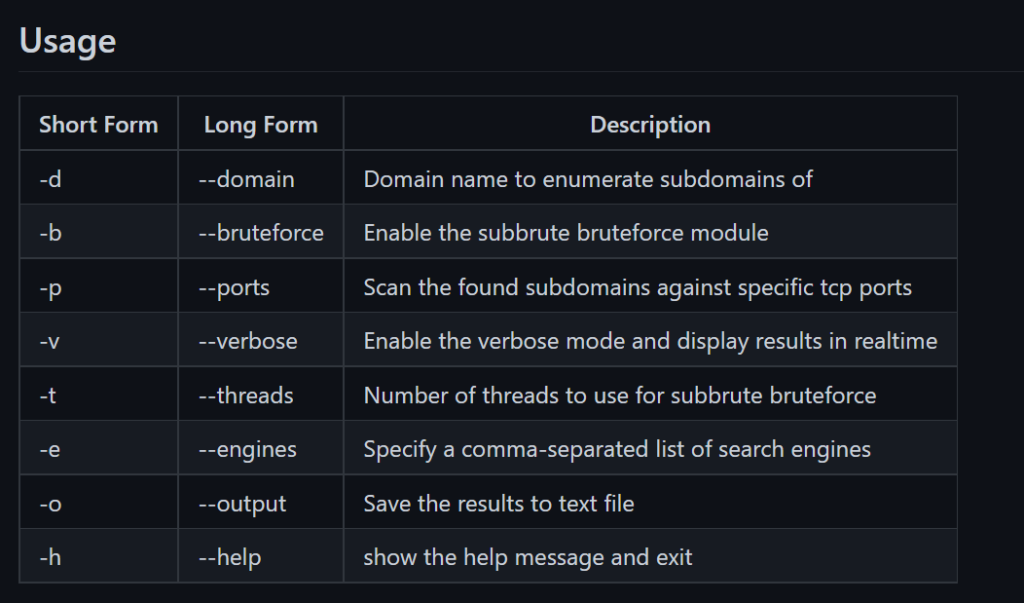
URL : https://github.com/aboul3la/Sublist3r
Help Page:
┌──(kali㉿kali)-[~]
└─$ sublist3r -h
Example:
┌──(kali㉿kali)-[~/Downloads/tools/Sublist3r]
└─$ sublist3r -d yahoo.com -vvvvvv
Google Dorks
Google Dorks is a term used to describe advanced search queries that use a special syntax to filter search results on Google. These queries are often used by security researchers and white hat hackers to find information that is not easily accessible through normal search queries.
Some examples of Google Dorks include:
- inurl:file_name.extension – This search query will return results that contain the specified file name and extension in the URL.
- site:example.com – This search query will return results from the specified website.
- filetype:extension – This search query will return results that have the specified file extension.
Google Dorks can be helpful for finding specific types of information on the internet, such as vulnerable websites, sensitive documents, and other resources that may not be easily accessible through normal search queries. They can also be used by attackers to find information that can be used in phishing attacks or other types of cyber attacks. It is important to use caution when using Google Dorks, as they can also potentially expose sensitive information or compromise the security of a website.
URL : https://www.exploit-db.com/google-hacking-database
Examples:
site: *.ine.com
site: *.ine.com intitle:admin
site: ine.com inurl:admin
site: *.ine.com filetype:pdf
intile:index of
cache:ine.com
inurl:auth_user_file.txt
inurl:passwd.txtEmail Harvesting With theHarvester tool
Email harvesting is the process of collecting email addresses from various sources, such as websites, social media platforms, and databases. It is often used by attackers to gather a list of potential targets for spamming or phishing attacks. For example, an attacker could use email harvesting to gather a list of email addresses that are associated with a particular company or organization, and then use this list to launch a targeted phishing attack.
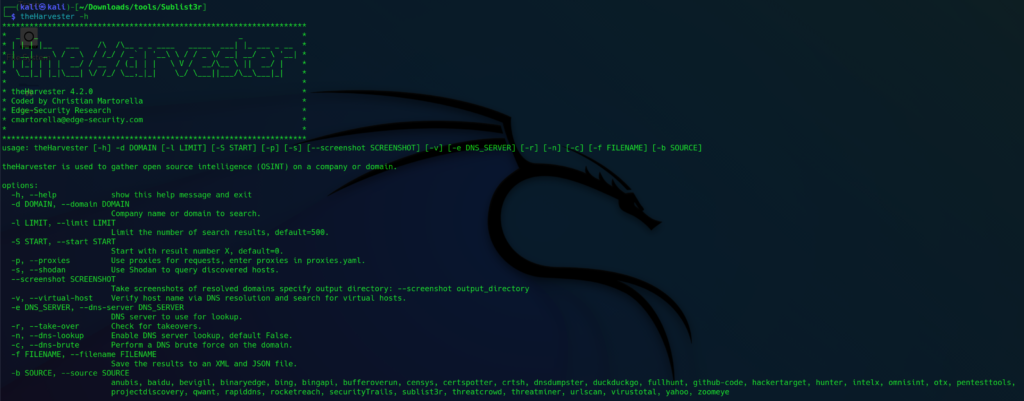
Email Harvesting With theHarvester tool:
theHarvester is a simple to use, yet powerful tool designed to be used during the reconnaissance stage of a red
team assessment or penetration test. It performs open source intelligence (OSINT) gathering to help determine
a domain's external threat landscape. The tool gathers names, emails, IPs, subdomains, and URLs by using
multiple public resources that include:
https://github.com/laramies/theHarvester
Help Page:
──(kali㉿kali)-[~]
└─$ theHarvester -h
Example :
┌──(kali㉿kali)-[~]
└─$ theHarvester -d zonetransfer.me -b baidu,bing
┌──(kali㉿kali)-[~]
└─$ theHarvester -d zonetransfer.me -b baidu 
Check for Leaked Password Databases
Check if email credential is leaked in data breach
Use:
https://haveibeenpwned.com/



















